| Name | Security Score | Audits | Price / 24h % | Market Cap | Ecosystem | Category | Badge & Honor |
|---|---|---|---|---|---|---|---|
 Particle Network Particle Network | 90 .71 AA | N/A | N/A | Web3 4 | 4 | ||
 1inch Network 1inch Network | 94 .12 AAA | $0.42 0.03% | $486M | 3 | DeFi 4 | 3 | |
 Nested Finance Nested Finance | 83 .76 A | N/A | N/A | 6 | DeFi 2 | ||
 The Guild The Guild | 78 .15 BBB | N/A | N/A | Marketplace 2 | |||
 Covalent Covalent | 92 .01 AA | $0.21 -0.04% | $145M | 9 | DeFi 4 | ||
 Celer Network Celer Network | 91 .69 AA | $0.027 0.04% | $210M | 7 | L2 Scaling 3 | 3 | |
 OKX Web3 OKX Web3 | 75 .80 BBB | N/A | N/A | 5 | NFT 2 | ||
 Rubic Rubic | 91 .17 AA | $0.033 -0.03% | $5.5M | 7 | DeFi 2 | 3 | |
 Cartesi Cartesi | 91 .12 AA | $0.2 0.02% | $159M | 5 | DeFi 3 | ||
 P2PBET P2PBET | 70 .02 BB | N/A | N/A | 3 | Gaming 2 | ||
 TrueUSD TrueUSD | 90 .16 AA | $1 0.00% | $510M | 9 | Stablecoin 2 | ||
 Coinsender Coinsender | 72 .09 BBB | N/A | N/A | 9+ | Lending & Borrowing 6 | ||
 TrustSwap TrustSwap | 89 .84 AA | $0.16 -0.02% | $16M | 4 | DeFi 4 | ||
 Aave Aave | 89 .40 AA | $86 0.01% | $1.3B | 5 | DeFi 5 | 3 | |
 Ampleforth Ampleforth | 89 .09 AA | $1 0.01% | $29M | 3 | DeFi 3 | 3 |
| Name | Security Score | Audits | Price / 24h % | Market Cap | Ecosystem | Category | Badge & Honor |
|---|---|---|---|---|---|---|---|
 Particle Network N/A | 90 .71 AA | N/A | N/A | 9+ | Web3 4 | 4 | |
 1inch Network $486M | 94 .12 AAA | $0.42 0.03% | $486M | 3 | DeFi 4 | 3 | |
 Nested Finance N/A | 83 .76 A | N/A | N/A | 6 | DeFi 2 | ||
 The Guild N/A | 78 .15 BBB | N/A | N/A | Marketplace 2 | |||
 Covalent $145M | 92 .01 AA | $0.21 -0.04% | $145M | 9 | DeFi 4 | ||
 Celer Network $210M | 91 .69 AA | $0.027 0.04% | $210M | 7 | L2 Scaling 3 | 3 | |
 OKX Web3 N/A | 75 .80 BBB | N/A | N/A | 5 | NFT 2 | ||
 Rubic $5.5M | 91 .17 AA | $0.033 -0.03% | $5.5M | 7 | DeFi 2 | 3 | |
 Cartesi $159M | 91 .12 AA | $0.2 0.02% | $159M | 5 | DeFi 3 | ||
 P2PBET N/A | 70 .02 BB | N/A | N/A | 3 | Gaming 2 | ||
 TrueUSD $510M | 90 .16 AA | $1 0.00% | $510M | 9 | Stablecoin 2 | ||
 Coinsender N/A | 72 .09 BBB | N/A | N/A | 9+ | Lending & Borrowing 6 | ||
 TrustSwap $16M | 89 .84 AA | $0.16 -0.02% | $16M | 4 | DeFi 4 | ||
 Aave $1.3B | 89 .40 AA | $86 0.01% | $1.3B | 5 | DeFi 5 | 3 | |
 Ampleforth $29M | 89 .09 AA | $1 0.01% | $29M | 3 | DeFi 3 | 3 |
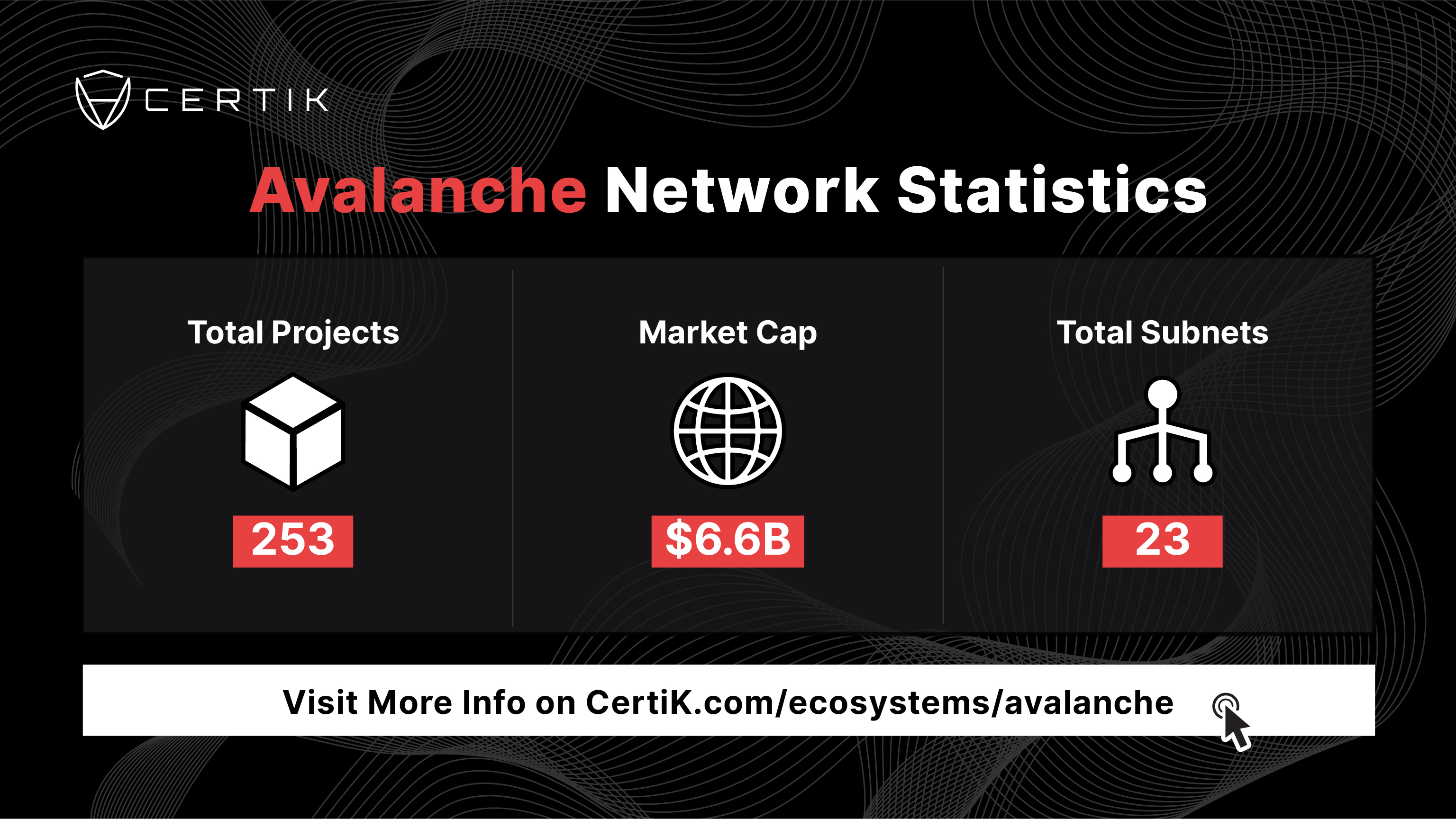
The growth of the Avalanche ecosystem over the last two years has been phenomenal. Yet the continued growth of Avalanche depends on its security growing in tandem with it. This means fostering an ecosystem that is filled with Avalanche projects that are as innovative as they are stable.
To that end, CertiK’s collection of security tools, from Avalanche smart contract audits and KYC verification, to blockchain analytics tools like Skynet are the ultimate toolkit for helping Avalanche projects achieve their full potential.
Reach out to the CertiK team to take the next step in securing your project.

CertiK offers the best security for Avalanche projects. With a growing roster of some of the best known Avalanche projects as our clients including Aave, 1inch, and Frax. Our in-depth understanding of Avalanche allows us to spot vulnerabilities and attack vectors that even the most dilligent developer may miss. Get in touch with us today to learn how CertiK can provide avalanche smart contract audits, as well as unparalleled, end-to-end security for your project.