Introduction
On 13 November, 2022 at 03:31:28 PM +UTC the CertiK Skynet system alerted a suspicious price slippage on the Flare token of over 63%. Following our investigation, CertiK determined that the Flare token project had conducted an exit scam by taking advantage of the initial token distribution. Flare Token was created on 2 October at 07:06:49 AM +UTC, 42 days before the exploit. At the time of the exploit, Flare token had approximately 15,246 holders.
It is unclear what the token was designed to do as there are no social media accounts or coverage of the project discovered thus far. The exploiter received 3,973,277,600.69 Flare tokens from Flare token deployer and associated addresses. The exploiter stole approximately $18.5 million in holders funds.
Attack Flow
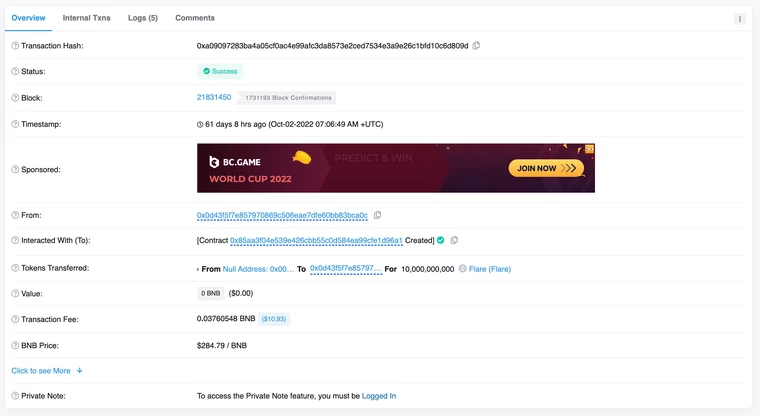
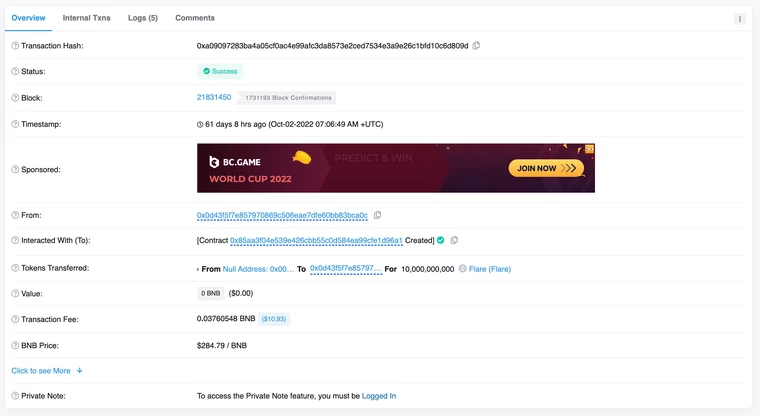
The Flare deployer minted 10,000,000,000 Flare token when deploying the Flare token smart contract:
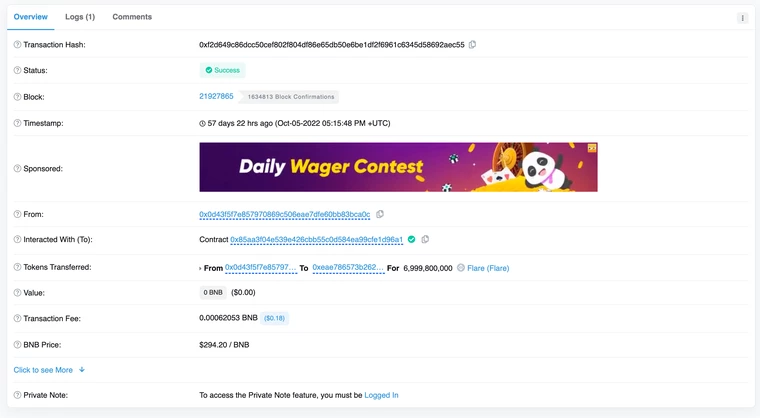
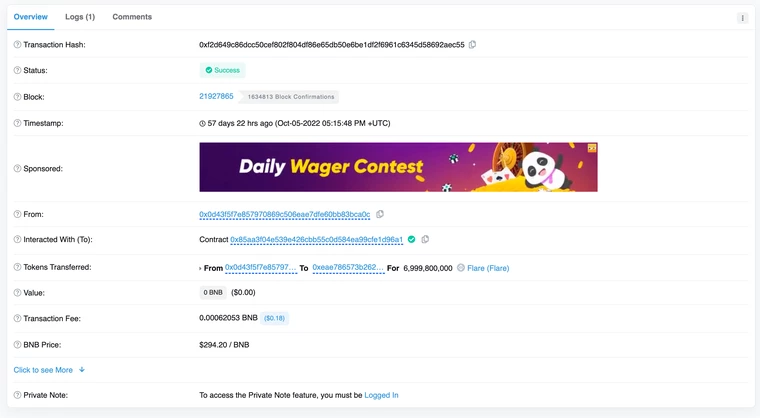
The Flare deployer then transfers 6,999,800,000 Flare tokens to an unverified smart contract 0xeae:
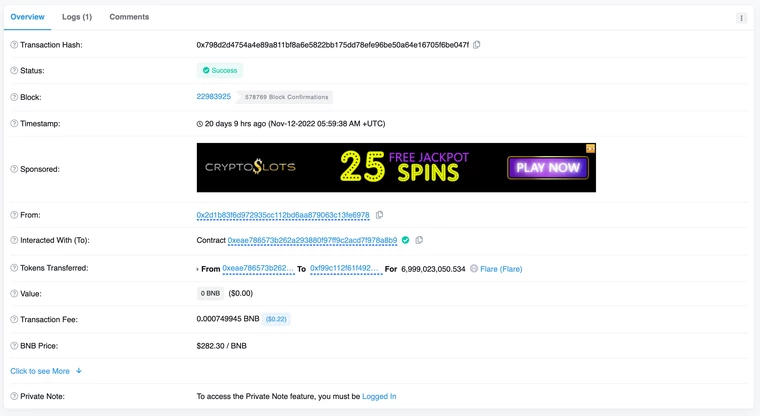
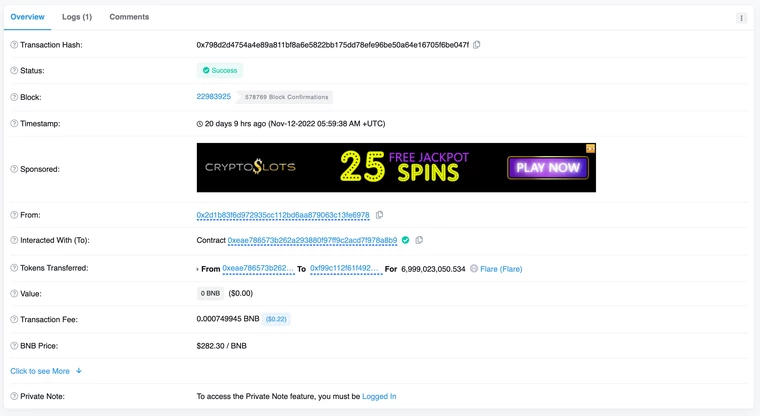
Deployer of unverified smart contract transfers 6,999,023,050.53 Flare tokens to 0xf99:
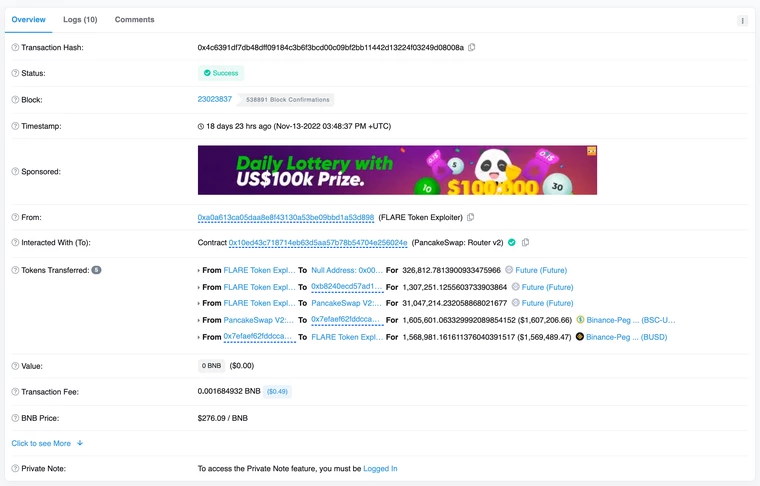
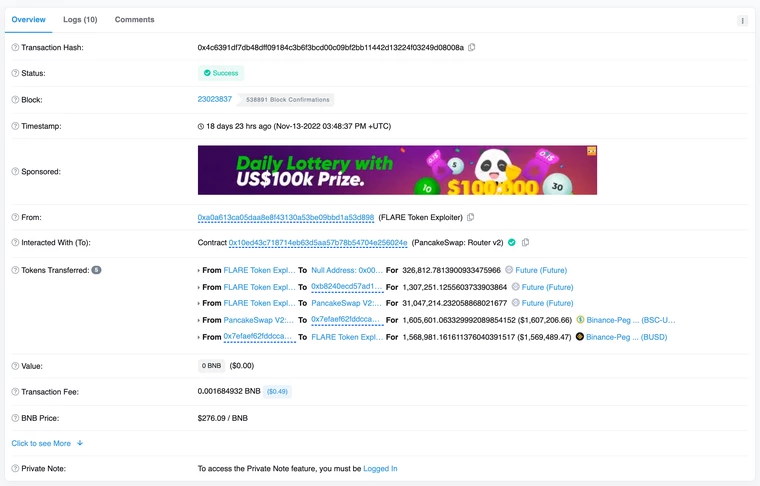
0xa0a swaps 1,000,000,000 Flare tokens to 16,942,732.78 BUSD, and then swaps 1,973,277,600.69 Flare tokens to Future tokens.
0xa0a finally swaps 1,307,251.13 future tokens to 1,568,981.16 BUSD:
Addresses
Flare token contract: 0x85a
Flare token contract deployer: 0x0d4
Unverified smart contract used in the exploit: 0xeae
Deployer of unverified smart contract: 0x2d1
Exploiter: 0xa0a
Exploit Transactions
In this transaction, 0xa0a swaps Flare tokens to BUSD: https://bscscan.com/tx/0x2af9b1c4f4b063a31babe75d0a7ef711e063d7ecb10cb0ecd6f572c8971c1d51
0xa0a then swap Flare tokens to Future token: https://bscscan.com/tx/0x4cc3211b0b0e7d4b56a85047f23138fc31c60edd7ab754c0b1b47eb6ba73ac9c
Finally, 0xa0a swaps Future tokens to BUSD: https://bscscan.com/tx/0x4c6391df7db48dff09184c3b6f3bcd00c09bf2bb11442d13224f03249d08008a
Example of exploiter transferring funds to be sent to tornado cash:
Profits and Asset Tracing
At the time of writing, around 1,000,000,000 Flare tokens were swapped for 16,942,732.78 BUSD and another 1,973,277,600.69 Flare tokens were swapped to Future tokens. Future tokens were then swapped to 1,568,981.16 BUSD. The total stolen funds of this exploit is around $18.5 million. As 28 November, 0xe55 only holds a remaining 0.06 BNB.
Conclusion
It is almost certain that the Flare token was designed to be an exit scam from the beginning. The issue lies within intentional poor contract design and the initial token distribution created by the contract deployers.
Protect yourself and your assets by following @CertiKAlert on Twitter to stay up to date on all the latest Web3 security news, and visiting certik.com as part of your due diligence.
Do your own research and beware of scam tokens!