Incident Summary
On 15 July 2025, a malicious actor took advantage of a lack of input validation in Arcadia Finance’s Rebalancer contract to obtain assets by paying off a portion of a user’s debt and withdrawing the underlying assets for a net gain of ~$3.6M.
 The root cause is due to the exploiter crafting arbitrary swapData. The stolen funds are currently held on Ethereum.
The root cause is due to the exploiter crafting arbitrary swapData. The stolen funds are currently held on Ethereum.
Vulnerability
Rebalancers manage concentrated liquidity positions dynamically, solving the challenge of maintaining optimal liquidity ranges in rapidly changing market conditions.
https://docs.arcadia.finance/protocol/asset-managers/rebalancers

Rebalancer.executeAction is only callable by an Account, whileAccount.flashAction is only callable by the Rebalancer.
The vulnerability is in unvalidated arbitrary calldata in the following call chain
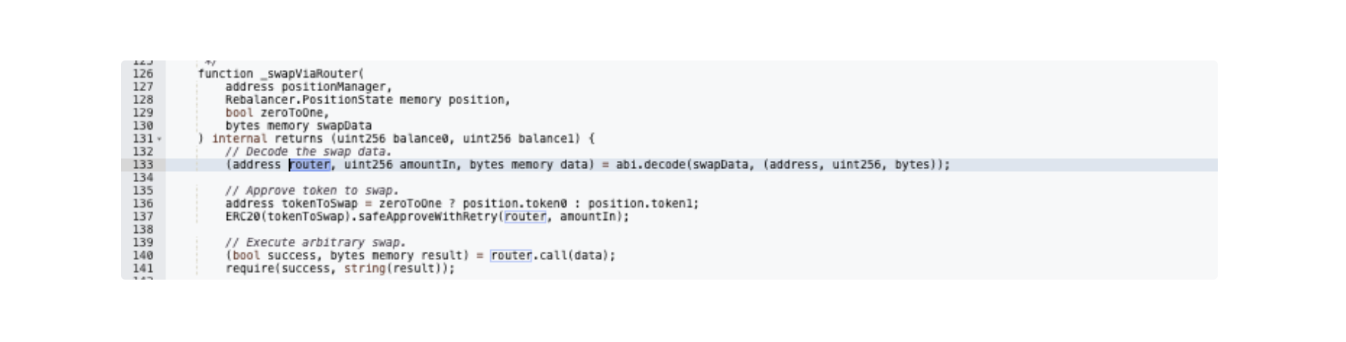
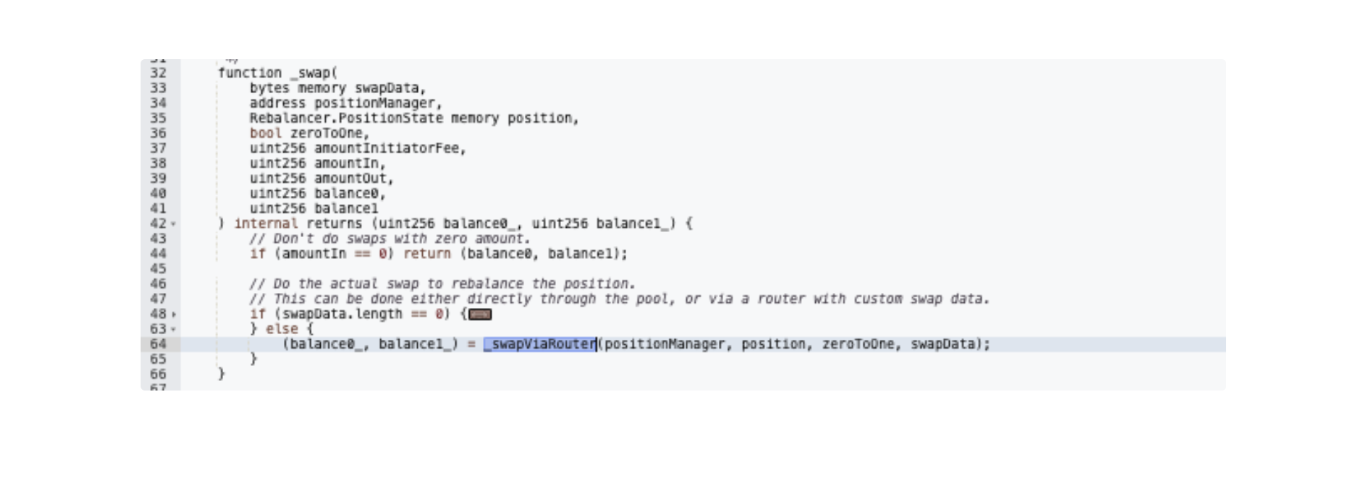
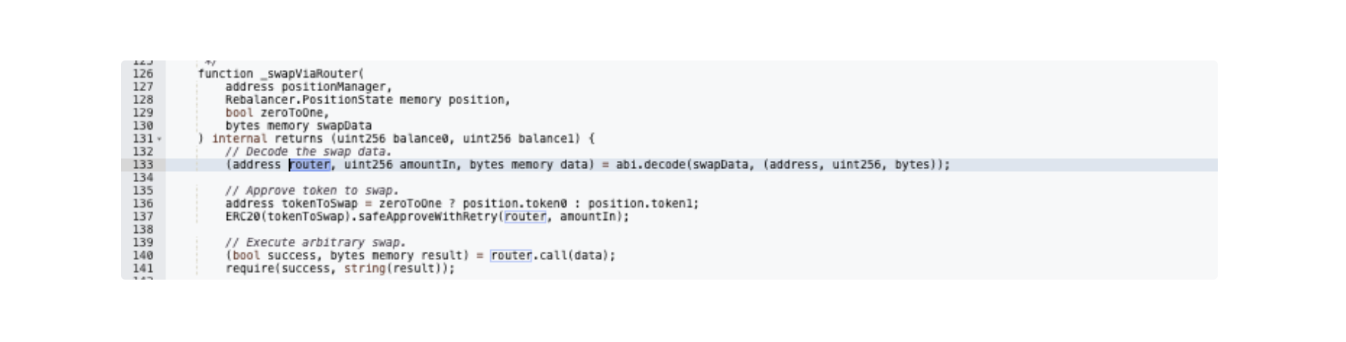
RebalancerSpot.rebalance() -> AccountV1.flashAction() -> actionTarget.executeAction()->_swap() -> _swapViaRouter() ->router.call(data)
Nowhere in the above call chain are the parameters that are decoded from swapData, in particular actionTarget and router addresses, examined.
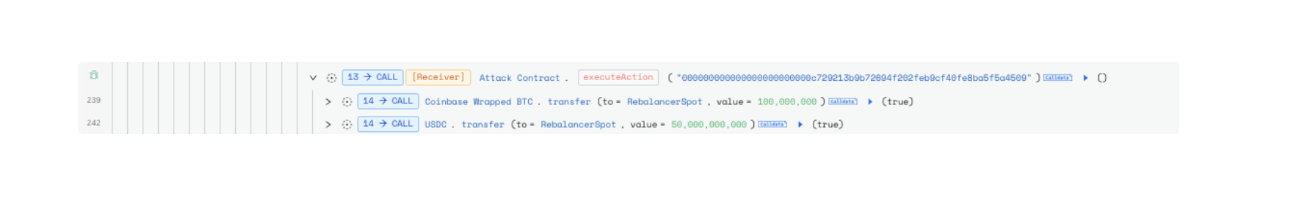
In this series of exploits, actionTarget is configured to be RebalanceSpot for reentrancy while router target the victim account and execution of data by the rebalancer drains the victim account.
Key Transactions
https://basescan.org/tx/0x06ce76eae6c12073df4aaf0b4231f951e4153a67f3abc1c1a547eb57d1218150
https://basescan.org/tx/0x0b9bed09d241cef8078e6708909f98574c33ee06abcc2f80bc41731cd462d60b
https://basescan.org/tx/0x9b55cc801bbd52d958b18a99d8e243e247429fb24c4ac39475e5e0ee94d13027
Attack Flow
Addresses
Exploiter:
- Wallet: 0x0fa54E967a9CC5DF2af38BAbC376c91a29878615
- Contract: 0x6250DFD35ca9eee5Ea21b5837F6F21425BEe4553/0x1DBC011983288B334397B4F64c29F941bE4DF265
- Fake account: 0xa6c64642b546026c768d3c20ab9d2bcbbad88712
Arcadia:
- Account: 0x9529e5988ced568898566782e88012cf11c3ec99
- AccountV1: 0xbea2B6d45ACaF62385877D835970a0788719cAe1
- RebalancerSpot: 0xc729213b9b72694f202feb9cf40fe8ba5f5a4509
Initial Setup
Prior to the exploit transaction, the exploiter created 15 Arcadia accounts: https://basescan.org/tx/0xeb1cbbe6cf195d7e23f2c967542b70031a220feacca010f5a35c0046d1a1820a
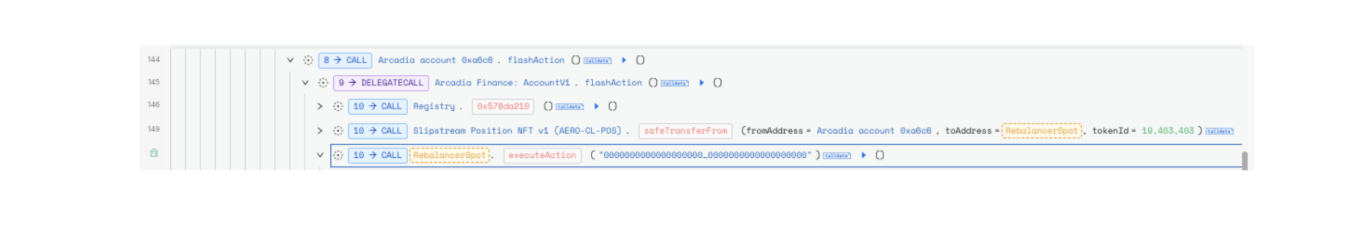
Step by Step Example based on exploit transaction: https://skylens.certik.com/tx/base/0x06ce76eae6c12073df4aaf0b4231f951e4153a67f3abc1c1a547eb57d1218150
- Flashloan 5,623 WETH and 9,968 CWBTC from Morpho.

- Set the AssetManager of the account 0xa6c6 to be RebalancerSpot and set the attack contract to be the account owner through RebalancerSpot.
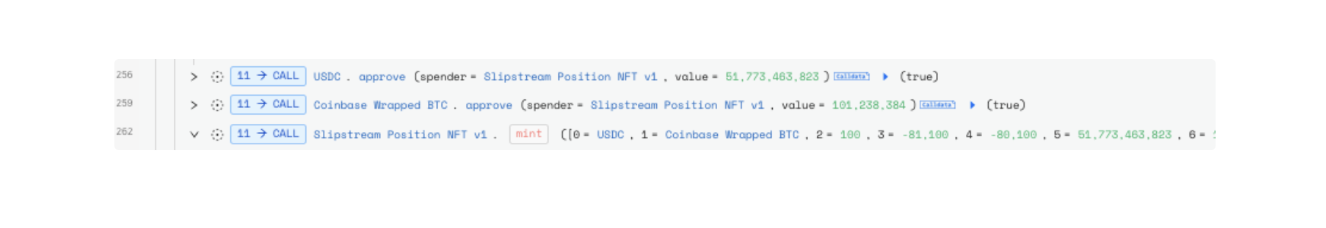
- Mint an LP NFT with 1,773 USDC and 0.123 Coinbase WBTC, then deposit LP NFT along with 10 USDC and 1 Coinbase WBTC into Arcadia Finance, as a pretense to the real action.
- Repay 14.4 WBTC ArcadiaV2 Coinbase Wrapped BTC Debt on behalf of account 0x9529e5988ced568898566782e88012cf11c3ec99, the target victim account.
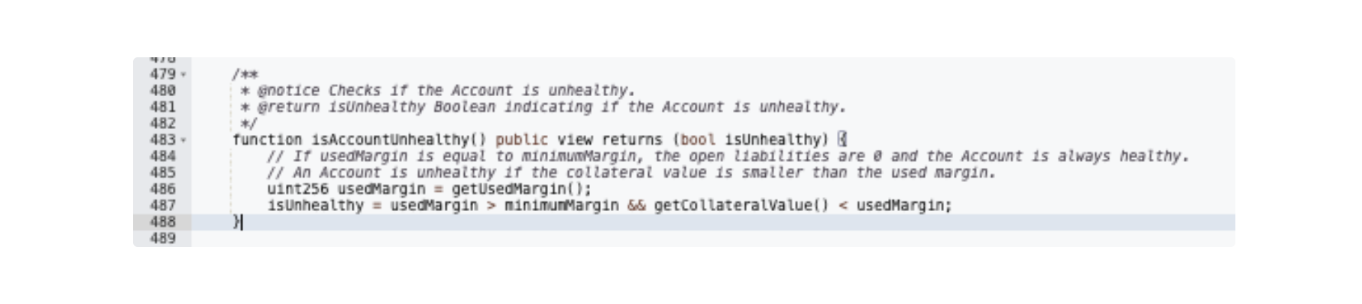
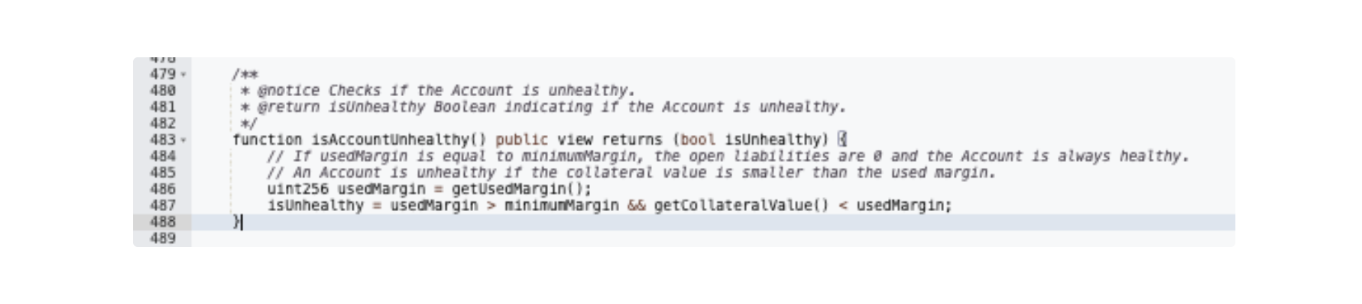
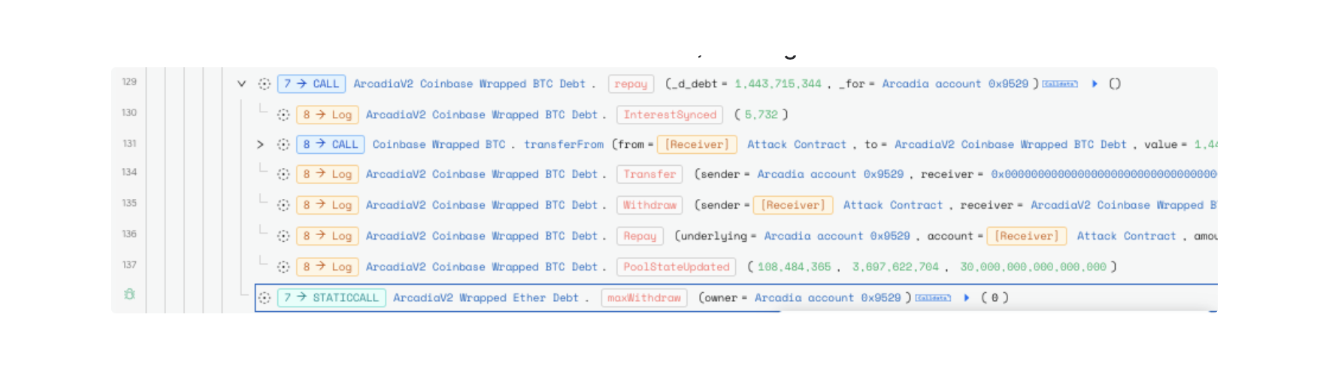 The repayment cleared the victim’s existing debt and will help to pass a health check in the AccountV1 contract after the theft.
The repayment cleared the victim’s existing debt and will help to pass a health check in the AccountV1 contract after the theft.
- Call RebalancerSpot.Rebalance(), with arbitrary swapData.
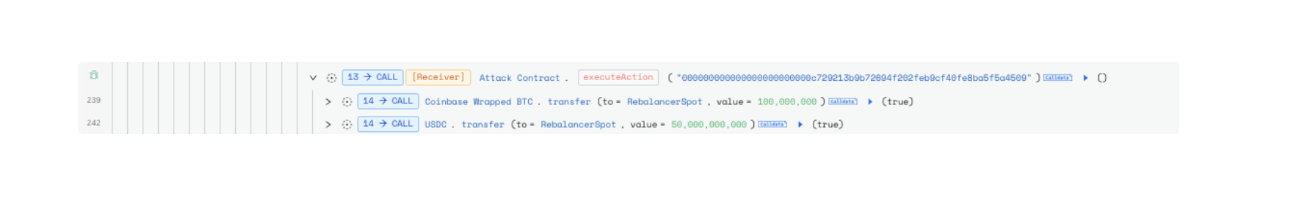
When calling rebalance(), the input account_ is set to 0xa6c64642b546026c768d3c20ab9d2bcbbad88712 (1 of 15 exploiter-deployed dummy accounts). During the rebalance() function, ‘actionData’ is executed.
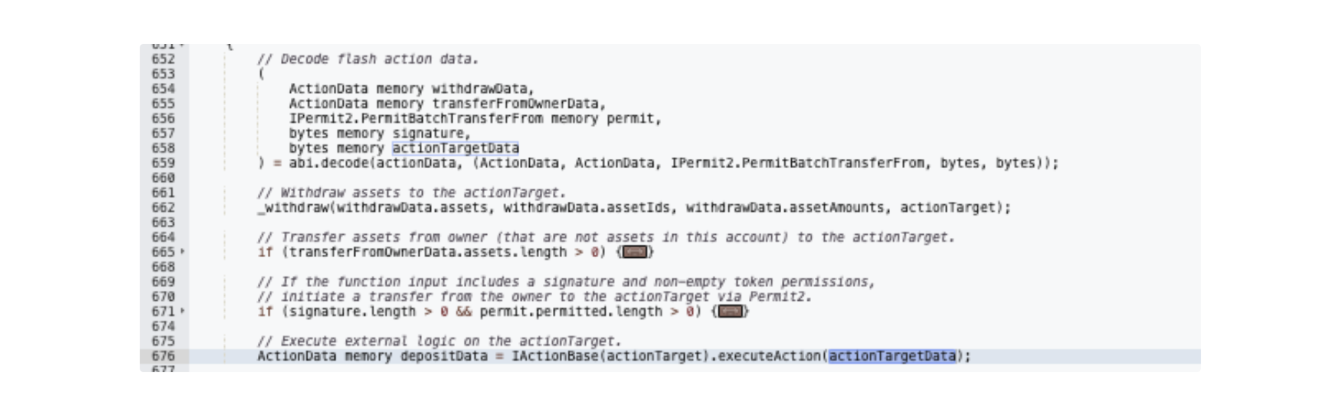
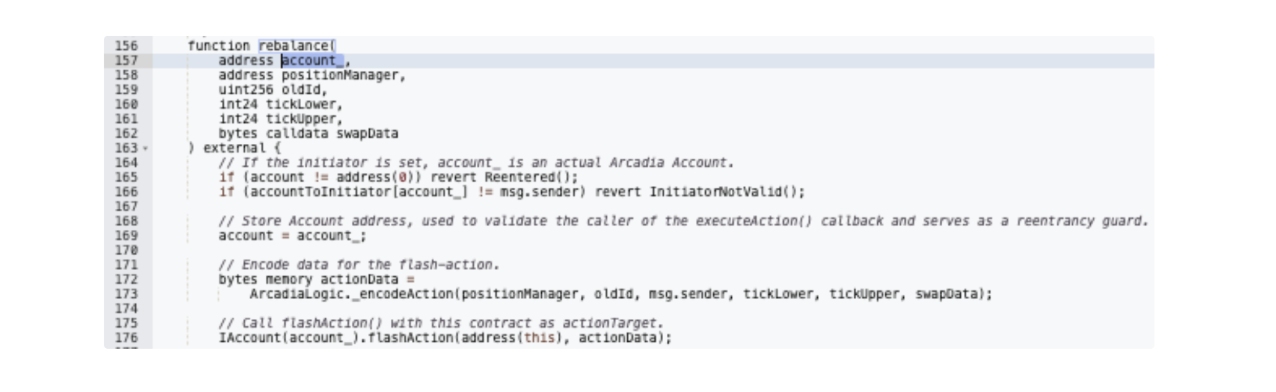 In this function, there is insufficient validation of either actionTarget and actionTargetData.
In this function, there is insufficient validation of either actionTarget and actionTargetData.
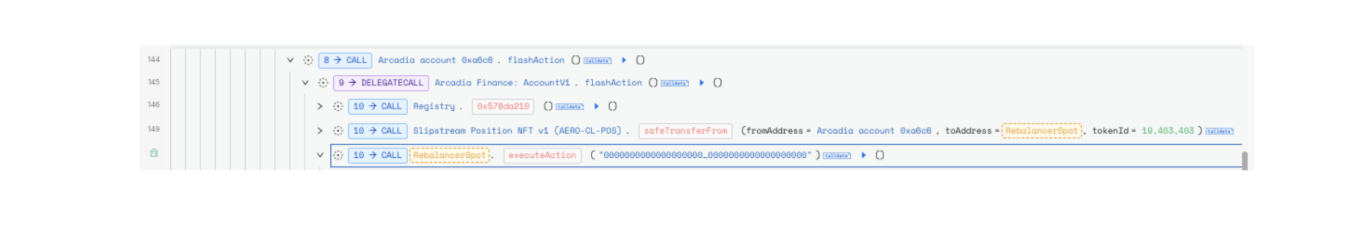 The exploiter is thus able to re-enter RebalanceSpot to execute the real operation.
The exploiter is thus able to re-enter RebalanceSpot to execute the real operation.

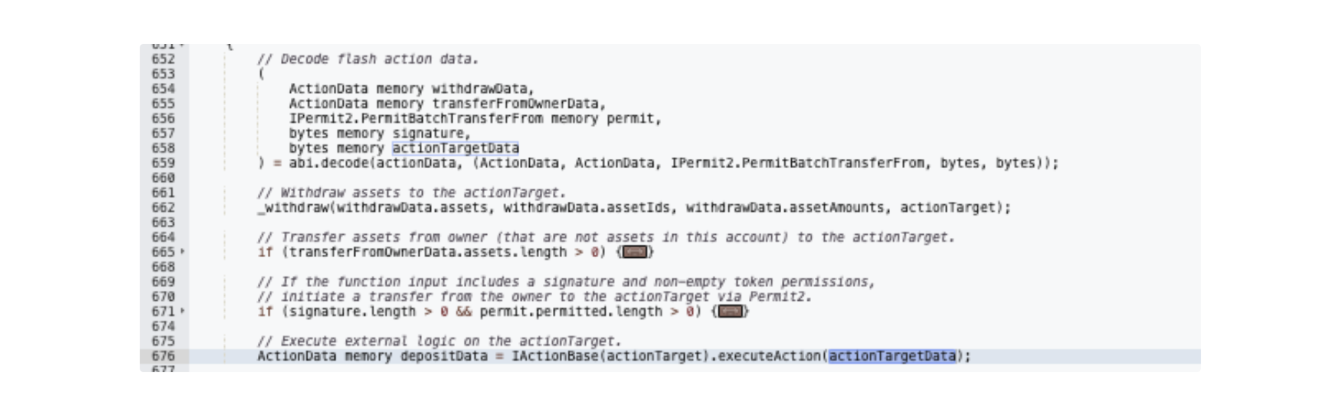
- They first removed LP and withdrew 1,773 USDC and 0.123 Coinbase WBTC to RebalancerSpot.
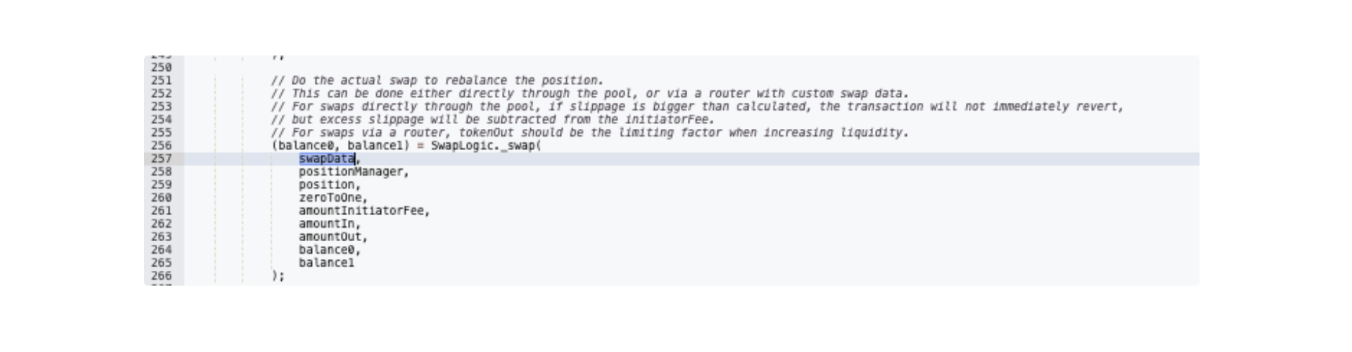 The rebalance.executeAction() executed SwapLogic._swap() which, in turn, called SwapLogic_swapRouter().
The rebalance.executeAction() executed SwapLogic._swap() which, in turn, called SwapLogic_swapRouter().
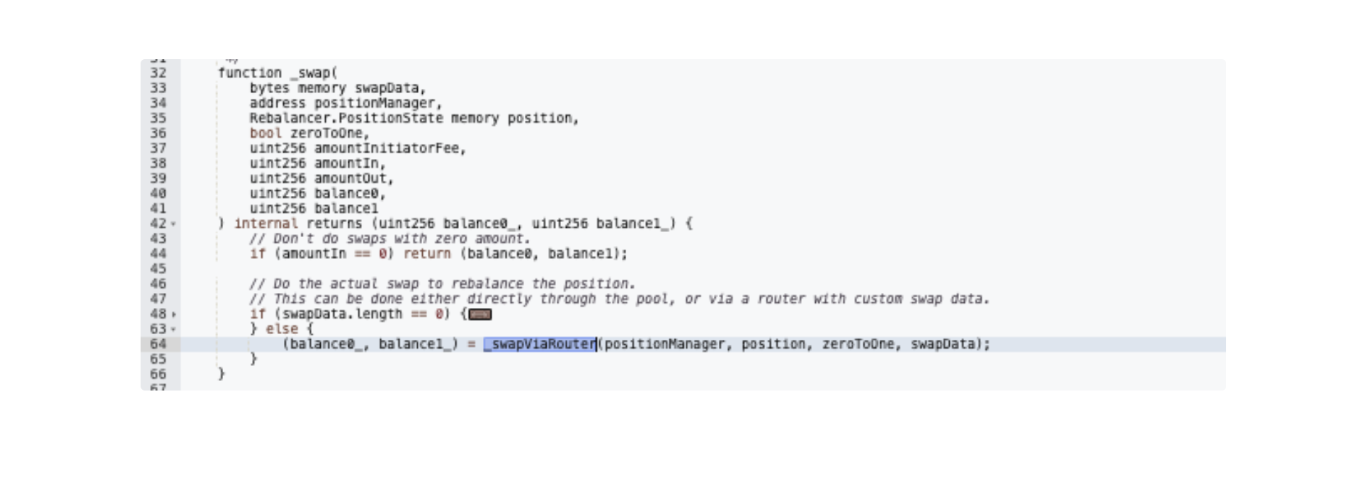 This’ router’ hidden deep in the initial swapData is decoded to be the target victim, account 0x9529.
This’ router’ hidden deep in the initial swapData is decoded to be the target victim, account 0x9529.
 And from it, flashAction() is executed where 15.7K USDC, 821 USDS Stablecoin, 964 Aerodrome, and the LP NFT StakedSlipstreamAM (id = 18906296) were transferred to the attacker.
Finally, the exploiter donated to RebalancerSpot 50K USDC and 1 Coinbase WBTC
And from it, flashAction() is executed where 15.7K USDC, 821 USDS Stablecoin, 964 Aerodrome, and the LP NFT StakedSlipstreamAM (id = 18906296) were transferred to the attacker.
Finally, the exploiter donated to RebalancerSpot 50K USDC and 1 Coinbase WBTC
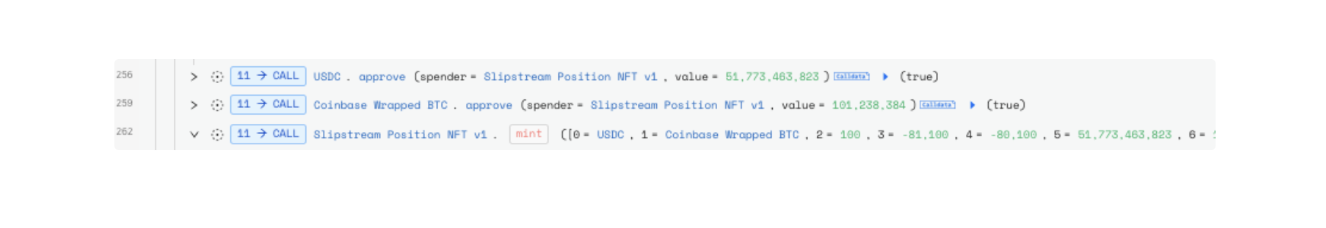 which was used to mint a Slipstream Position NFT v1
which was used to mint a Slipstream Position NFT v1
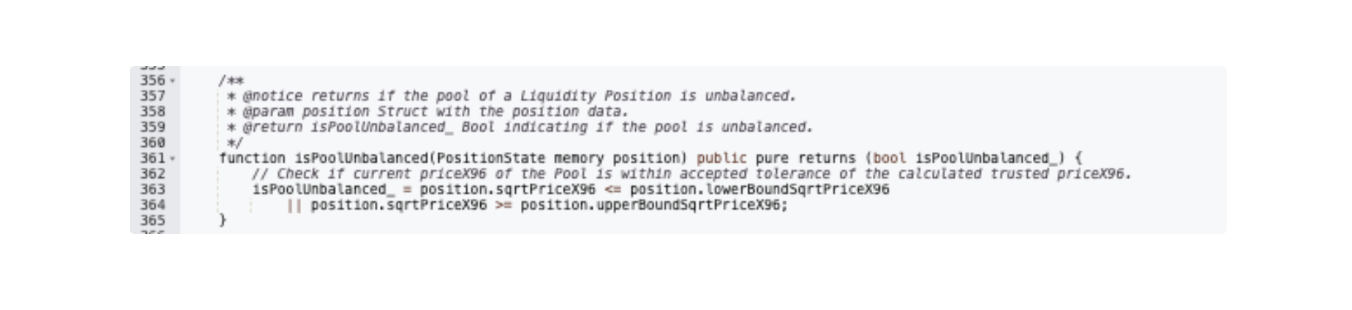
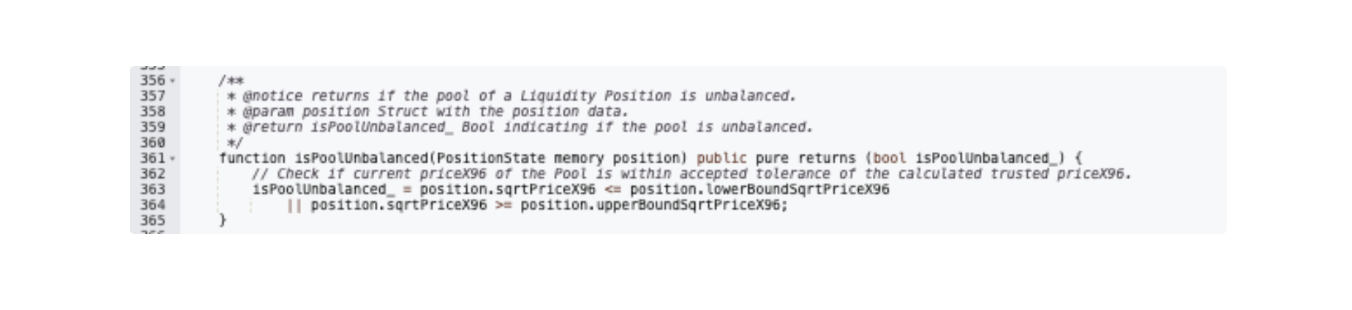
 as is needed to ensure the Pool was balanced
as is needed to ensure the Pool was balanced
- Withdraw the Slipstream Position NFT v1 (AERO-CL-POS) along with the remaining tokens.
- Remove the liquidity of LPs acquired, then repay flashloan.
Fund Flow
The exploiter’s wallet was funded by a Tornado Cash deposit 8 hours before the attack.
 The exploiter swapped stolen funds for 1,203 ETH (~$3,6M) in 1inch, then bridged the funds from Base to Ethereum network via Across Protocol and Relay.
The exploiter swapped stolen funds for 1,203 ETH (~$3,6M) in 1inch, then bridged the funds from Base to Ethereum network via Across Protocol and Relay.
 As of writing the stolen funds are held in wallet 0x0fa5 on Ethereum.
As of writing the stolen funds are held in wallet 0x0fa5 on Ethereum.
 The Arcadia team has reached out to the exploiter to offer a 10% bounty for the return of the remaining funds.
The Arcadia team has reached out to the exploiter to offer a 10% bounty for the return of the remaining funds.

To keep up to date on the latest incident alerts and statistics follow @certikalert on X, or read our latest analysis on certik.com.


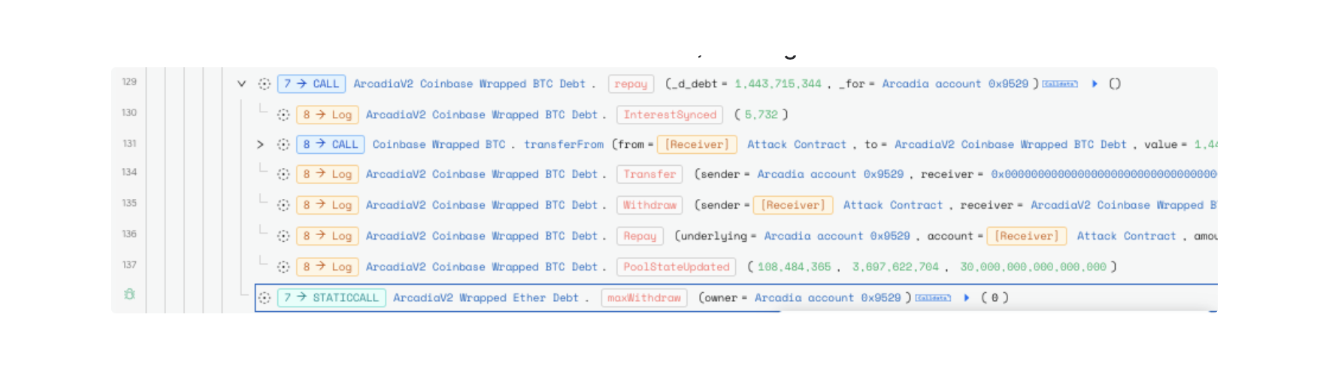 The repayment cleared the victim’s existing debt and will help to pass a health check in the AccountV1 contract after the theft.
The repayment cleared the victim’s existing debt and will help to pass a health check in the AccountV1 contract after the theft.
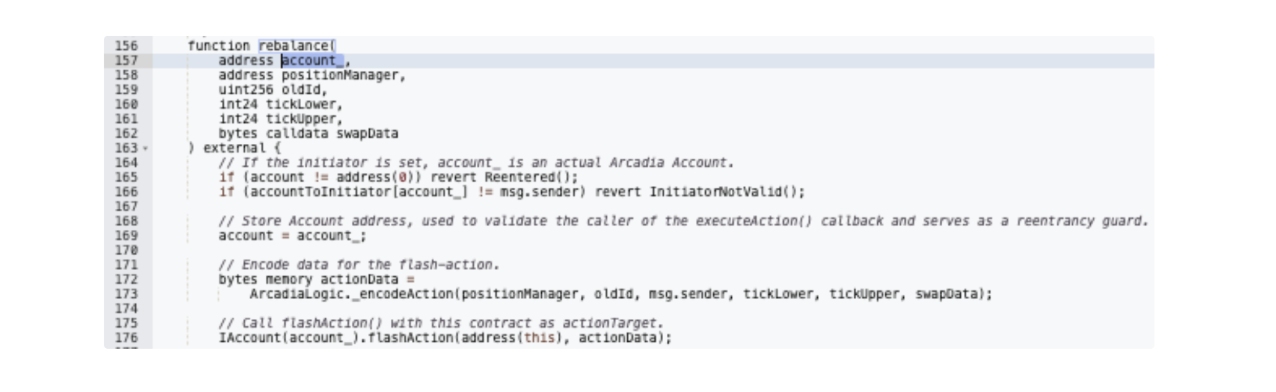 In this function, there is insufficient validation of either actionTarget and actionTargetData.
In this function, there is insufficient validation of either actionTarget and actionTargetData.
 The exploiter is thus able to re-enter RebalanceSpot to execute the real operation.
The exploiter is thus able to re-enter RebalanceSpot to execute the real operation.

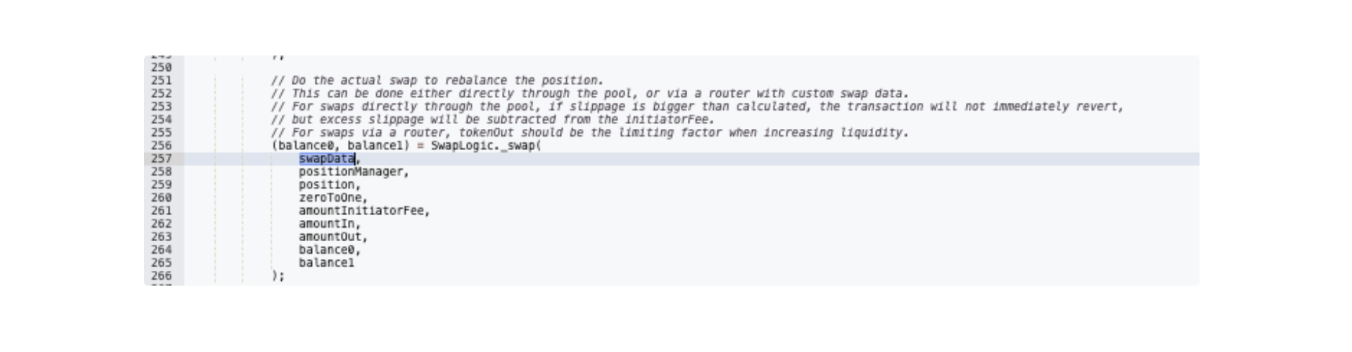 The rebalance.executeAction() executed SwapLogic._swap() which, in turn, called SwapLogic_swapRouter().
The rebalance.executeAction() executed SwapLogic._swap() which, in turn, called SwapLogic_swapRouter().
 This’ router’ hidden deep in the initial swapData is decoded to be the target victim, account 0x9529.
This’ router’ hidden deep in the initial swapData is decoded to be the target victim, account 0x9529.
 And from it, flashAction() is executed where 15.7K USDC, 821 USDS Stablecoin, 964 Aerodrome, and the LP NFT StakedSlipstreamAM (id = 18906296) were transferred to the attacker.
Finally, the exploiter donated to RebalancerSpot 50K USDC and 1 Coinbase WBTC
And from it, flashAction() is executed where 15.7K USDC, 821 USDS Stablecoin, 964 Aerodrome, and the LP NFT StakedSlipstreamAM (id = 18906296) were transferred to the attacker.
Finally, the exploiter donated to RebalancerSpot 50K USDC and 1 Coinbase WBTC
 which was used to mint a Slipstream Position NFT v1
which was used to mint a Slipstream Position NFT v1
 as is needed to ensure the Pool was balanced
as is needed to ensure the Pool was balanced