Project name: Swaprum
Project type: Staking
Date of exploit: May 18, 2023
Asset loss: $ 3,000,000
Vulnerability: Rugpull
Date of audit report publishing: May 5, 2023
Conclusion: Out of Audit Scope
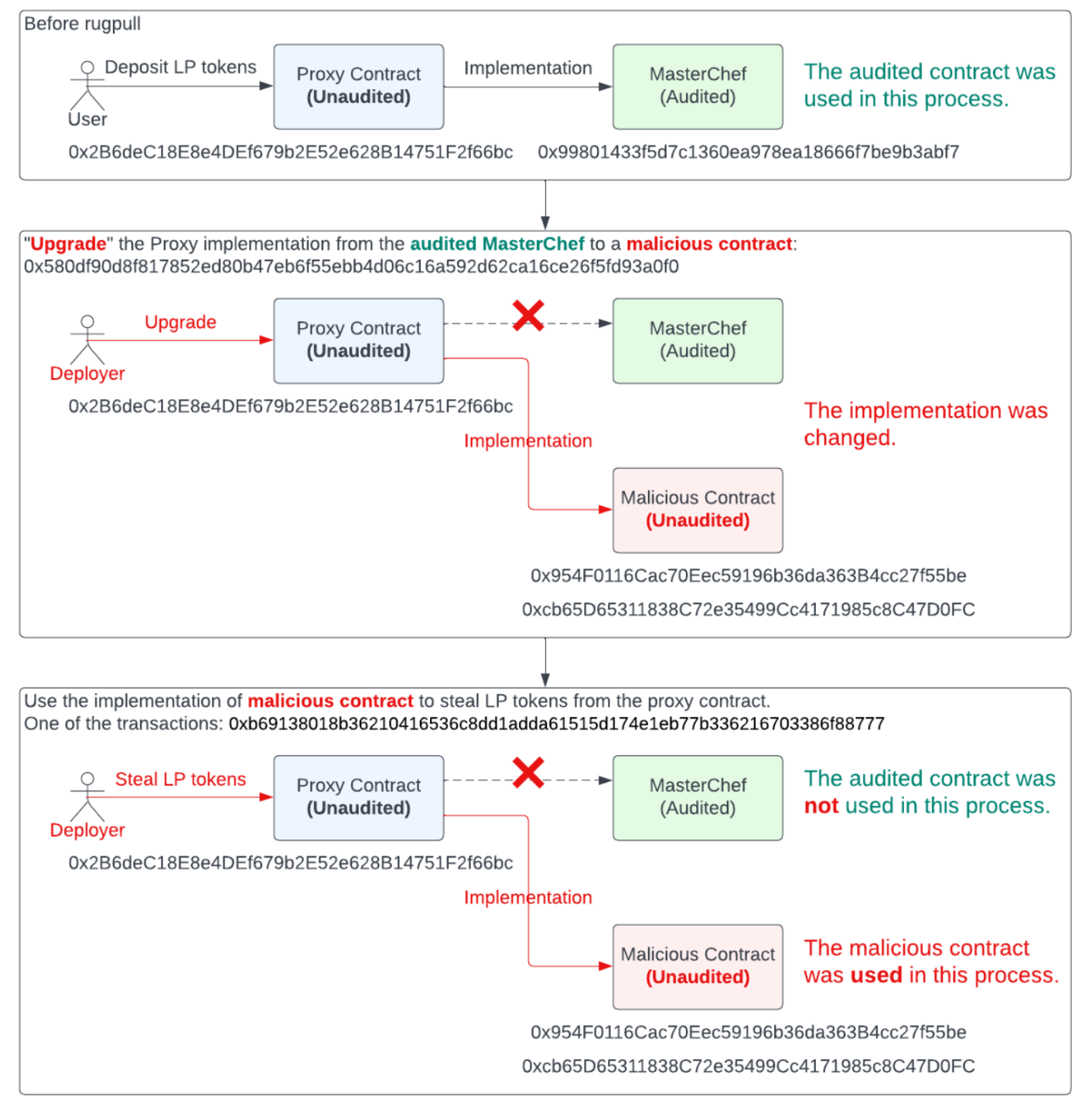
Details of the Exploit
Background
Swaprum project includes DEX and MasterChef-like staking contracts. Users can stake LP tokens into the MasterChef contract to get the reward.
Nature of the Vulnerability
- The masterchef-like staking contract is upgradeable.
- The project owner upgraded the staking implementation contract to a malicious version.
- In the updated implementation, the malicious function
add, which is different from the audited version, moves staked LP tokens and removes liquidity. A newly added functiongetTokenis invoked to mint Swaprum tokens for the deployer and sell them for profit.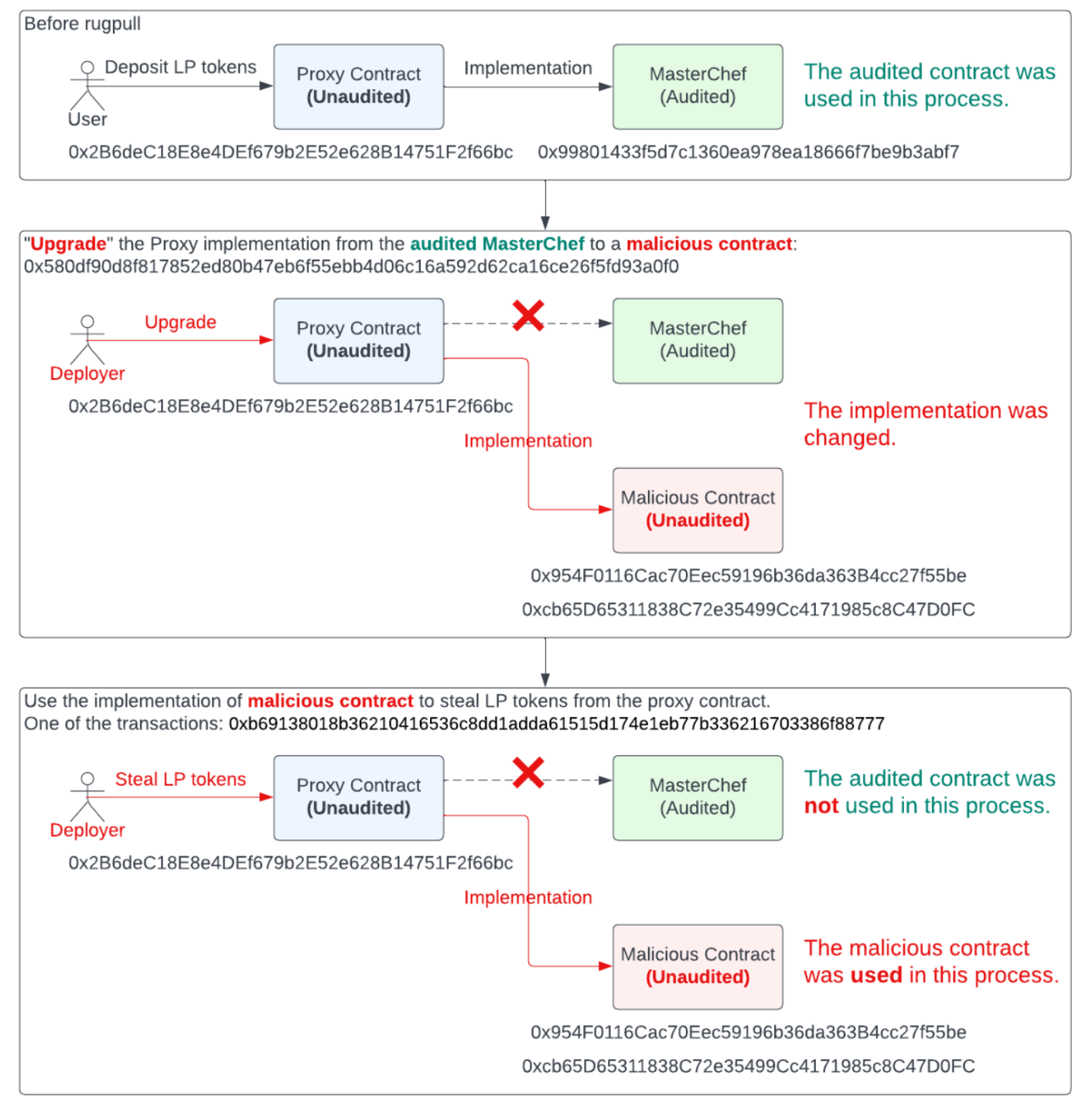
CertiK Audit Overview

Conclusion
On May 18, 2023, the Swaprum protocol deployer rug pulled by upgrading the contract “MasterChef” contract to the malicious version and withdrew a significant quantity of LP tokens that staked inside the contract and mint a large amount of Swaprum token to drain the pool.