Blockchain Bug Bounty
Crowdsourcing from a list of the world's top ethical hackers to provide you with continuous assessment for uncovering vulnerabilities before anyone else does.
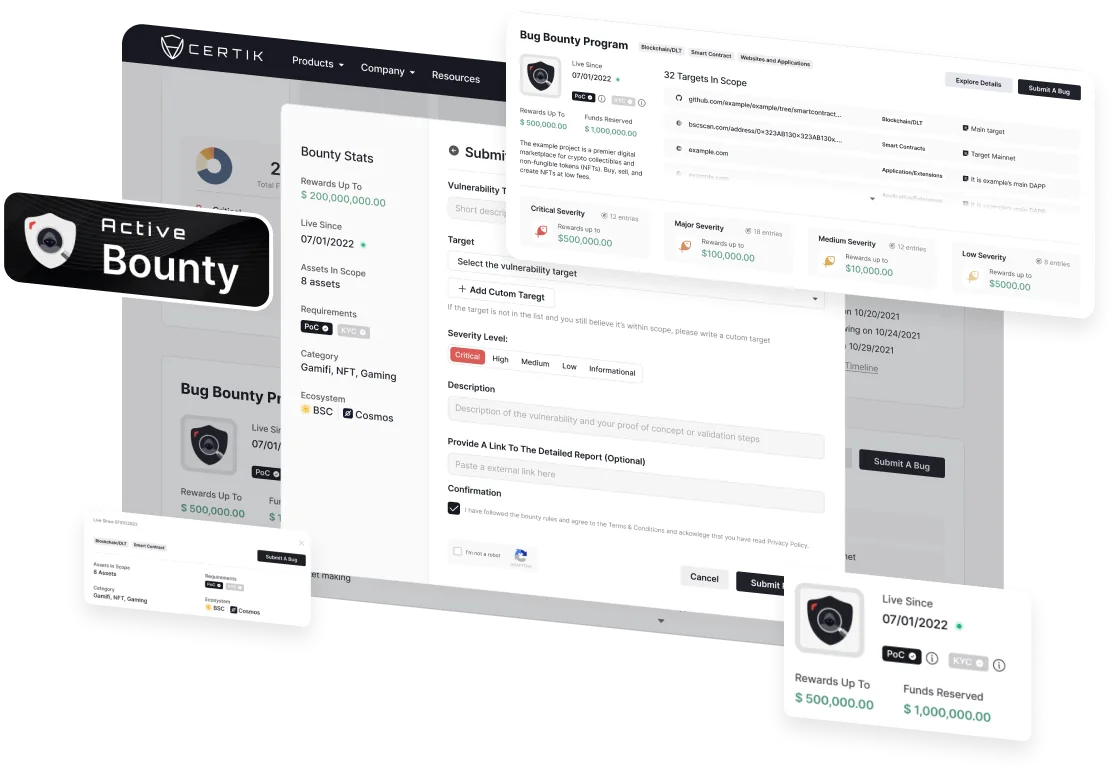
The CertiK Bug Bounty Platform
Combining years of Web3 security experience with a well-established technical community, CertiK’s Bug Bounty is the only Web3 platform providing fully managed end-to-end support with 0% fee on bounty payouts.
Submission Screening and Triage Support
Community-Focused Ethical Hackers
0% Fee on Bounty Payout
Peace of Mind for Your Project and Community
Setting up a bug bounty with CertiK enables projects to leverage the expertise of ethical hackers to further derisk their code against additional vulnerabilities.
Proactive Defense
White-hat ethical hackers with intuitive knowledge of the latest attacks can identify threats before malicious actors have the opportunity to exploit them.
Crowd-Sourced Security
Gain access to a highly skilled community of ethical hackers who specialize in different areas of vulnerability detection.
Expedited Submission Screening and Triage
Partner with CertiK security engineers who will rapidly review all your inbound bug submissions and help ensure the proper steps are taken to fix any issues.
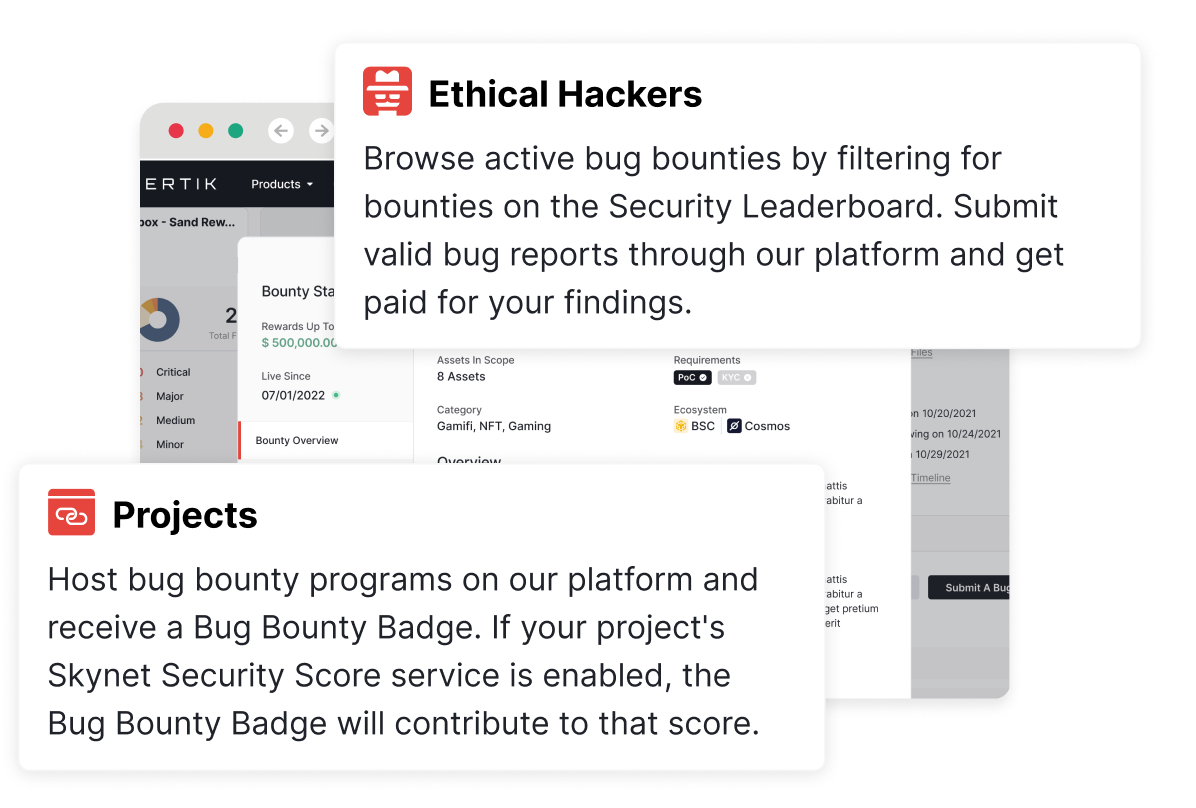
Integration with Skynet Trust Score
Bug bounty remediation of findings is integrated with Skynet and will improve your project's overall trust score.
The Next Step In Web3 Security
CertiK's bug bounty program offers a trusted platform for projects and ethical hackers to connect.
The Project
1. Get onboarded with a dedicated program manager.
2. Launch your program and activate your bounty badge on certik.com.
3. Receive submissions and pay bounties directly if qualified.
The Leaderboard User
1. Add projects with active bounty badges to your watchlist.
2. Strengthen your technical due diligence capabilities.
3. Evaluate projects with additional security measures.
The Ethical Hacker
1. Sign up for the platform and browse bounties.
2. Review in-scope assets and submit reports.
3. Get paid directly and gain your Web3 white hat reputation.
Working Together to Create a Safer Web3 Ecosystem
Web3, as well as associated Web2 components of projects, are increasingly under attack by malicious actors seeking to exploit security vulnerabilities in project code. These adversaries are always "one step ahead" of protecting these projects, constantly running reconnaissance and developing new attack vectors within the project’s threat landscape.