TL;DR
On October 11, 2022 at 6:19 PM EST, Mango Market was attacked, causing a loss of $116M. The attacker was able to manipulate the price of MNGO token and borrowed more assets on the platform than was permitted.
Introduction
Mango Market is built on the Solana blockchain and utilizes Serum DEX for spot margin trading while perpetual futures are traded on Mango Market’s own order book. Mango Market is governed by $MNGO token holders via the Mango DAO.
On October 11, 2022 at 10:19 PM UTC, Mango Markets was hacked by a group of attackers, including Avraham Eisenberg who claimed to be part of the group on Twitter. A loss of MNGO has dropped 47% as a result of the incident.
On October 15, 2022 Eisenberg posted on Twitter that this was a “highly profitable trading strategy” and that it was “legal open market actions, using the protocol as designed.” In his tweet, he claims that the development team failed to anticipate the consequences of the protocol’s parameters.
Funds Returned
The attacker submitted a proposal to send the token back. The wallet receiving funds drained from the protocol offered via a DAO community vote to return a portion of the proceeds less a substantial bounty, if the community promised not to pursue legal action.
On October 15, 2022 Mango’s developers tweeted that they were in the process of getting back $67 million in various cryptoassets and that the team started working on an algorithm to decide on a refund split. Overall, after a proposal in the Mango’s governance forum was approved, Eisenberg was allowed to keep $47 million as a “bug bounty” while $67 million was sent back to the treasury.
Eisenberg was initially linked to the wallet address that carried out the attack via an ENS domain name ponzishorter.eth. An anonymous Discord chat log also showed Eisenberg discussing the precise mechanism of the exploit in advance.
Attack Flow
- The attacker funded the first account (Account A) CQvKSNnYtPTZfQRQ5jkHq8q2swJyRsdQLcFcj3EmKFfX with 5M USDC in this transaction.

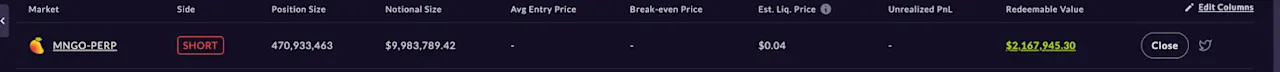
- The attacker then offered out 483M units of MNGO perps (short) on the order book
- The attacker funded the second account (Account B) 4ND8FVPjUGGjx9VuGFuJefDWpg3THb58c277hbVRnjNa

Then the second account was used to buy 483M units of MNGO perps (long), at a price of $0.0382 per unit.
The attacker started to move the spot price of MNGO, and increased it to $0.91

With MNGO/USD price of $0.91 per unit, account B was able to borrow other tokens on Mango Market. The attacker also used the funds in account B (the original deposit + the funds for selling borrowed MNGO) to borrow other tokens on Mango Market.
The above borrow behaviors leave account A with a total value of $11,306,771.61 uncollectible debt and account B with -$115,182,674.43 bad debt.
Addresses
Two accounts were used to conduct the attack.
Account “A” received 5M USDC collateral which offered out 483mm units of MNGO perps: CQvKSNnYtPTZfQRQ5jkHq8q2swJyRsdQLcFcj3EmKFfX
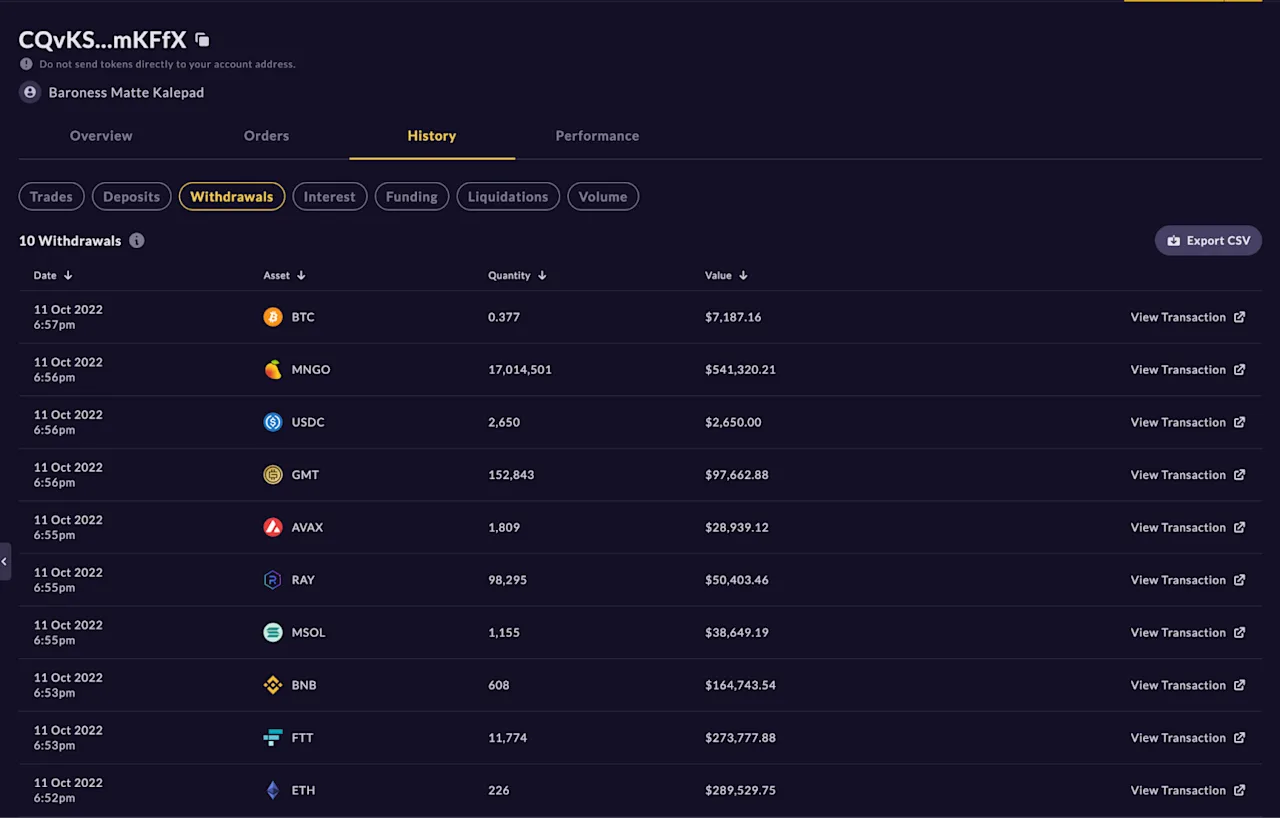
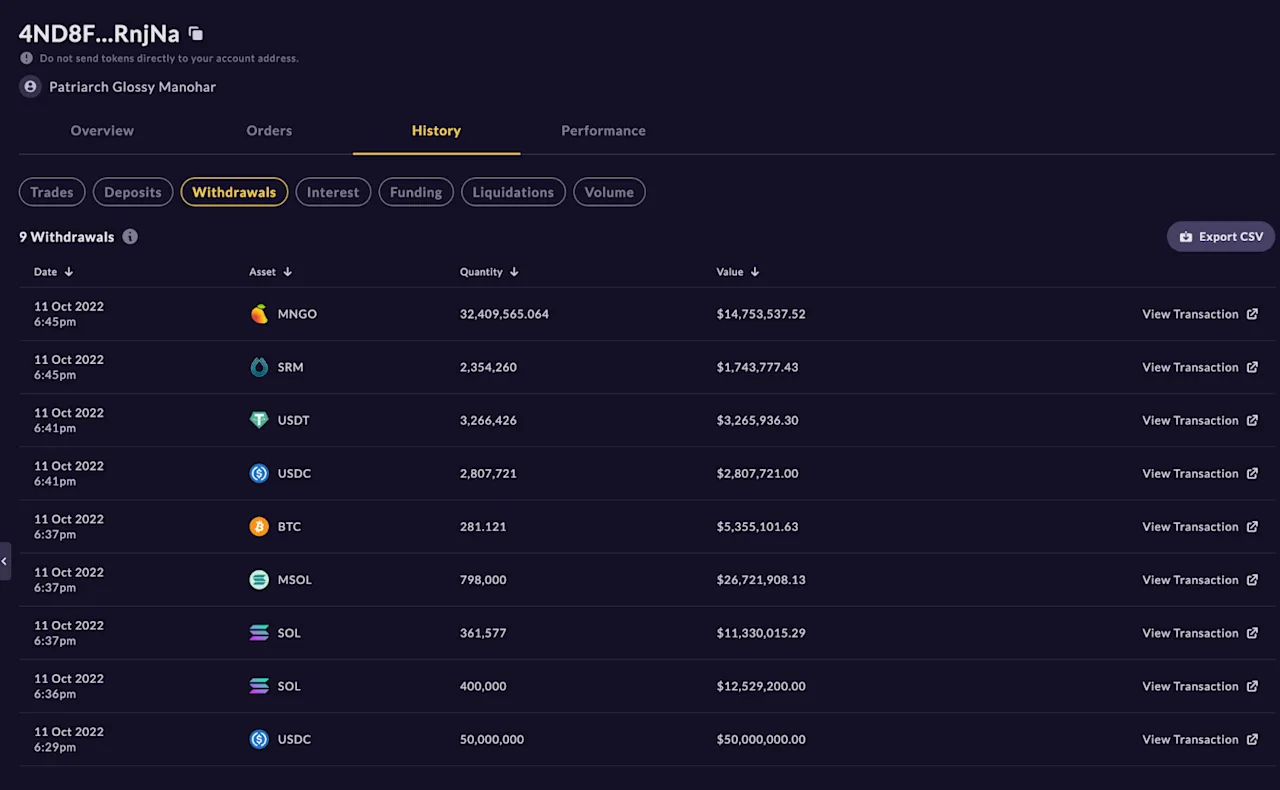
Account “B,” the trader, used another 5 million USDC to buy the same amount of MNGO, using 10 million USDC in total to effectively hedge his position: 4ND8FVPjUGGjx9VuGFuJefDWpg3THb58c277hbVRnjNa
Profit and Assets Tracing
Account A:
Account B:
Conclusion
Overall, the attackers executed a self-funded economic attack by manipulating the oracle price of MNGO. Since the attack, a debate has been sparked on Twitter as to whether those responsible could be subject to civil or even criminal liability. So far, there are few precedents for prosecuting this type of DeFi market manipulation. This case has some similarities to the Indexed Finance exploit that took place in December 2021. The founders of the protocol identified the attacker, and a lawsuit is still pending in Canadian courts. Following these events, Mango Markets has announced a new version dubbed 'v4' which will use the Serum Community Fork. Despite serious setback, the project appears hopeful in securing a place in the future of web3.
