Introduction
On 18 November 2023, Kronos Research announced, via social media platform X, that unauthorized access to their API resulted in a loss of approximately $26 million. The incident isn’t a typical private key compromise which often refers to the private key of a victims wallet, but instead was due to a API private key compromise. Whilst there are differences between the two, this incident resulted in the victim losing control of their funds. Since the API keys belonging to Kronos Research were compromised, we are classifying this incident as a private key compromise, which have seen $134 million lost in November alone.
Event Summary
Late evening on 18 November 2023 Kronos Research announced that they were investigating unauthorized access to their API key.
A look on chain at Kronos Ethereum wallet 0x6F15ee9258ACDEbf356dB7aB607bB255a00C6fdF showed that a number of USDT withdrawals had been made from Binance that that were then transferred to EOA 0x2b0502FDab4e221dcD492c058255D2073d50A3ae. Initially, at 16:47 UTC on 18 Nov, 0x6F1 withdrew 72 USDT from Binance, likely to test that the attacker had control. Fifteen minutes later a further 2.4 million USDT was withdrawn from Binance which was then transferred to 0x6F1.
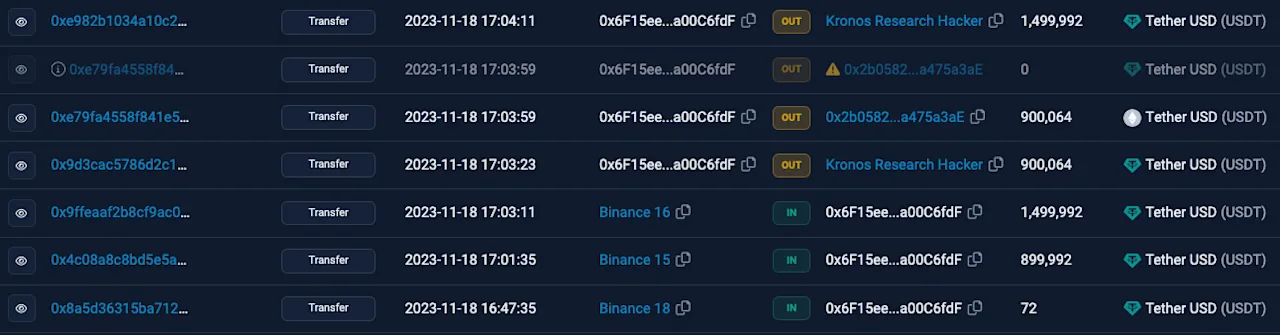
Over a three hour period, 22,899,712 USDT had been withdrawn from Binance and then transferred to 0x6F1.
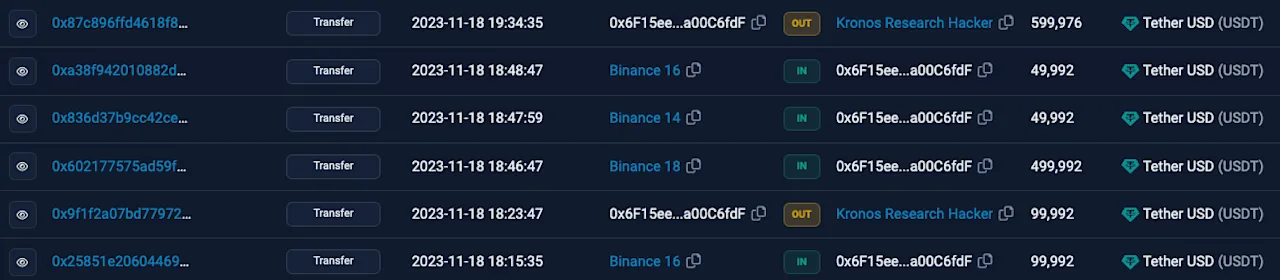
The attacker was also able to transfer assets on the BSC network which included $2 million of WOO tokens, $107k WBNB and $82k BNB. On 19 November Kronos confirmed on X that they had suffered losses of approximately $26 million.
Asset Tracing
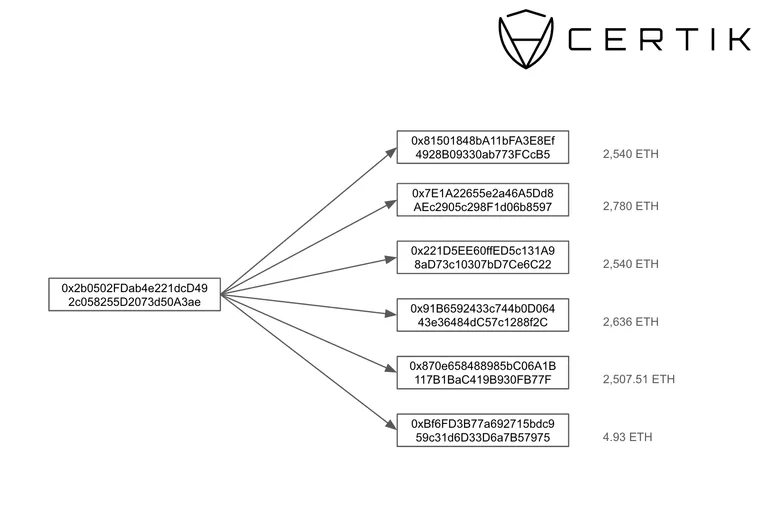
The Kronos Research exploiter consolidated all stolen funds from multiple chains on the Ethereum network, and distributed the funds to six wallets. In total, the attacker is in control of 13,008 ETH which at the time of writing is worth $26.2 million.
API Key Compromise
Application programming interface (API) facilitate the connections between two otherwise disconnected softwares. Many centralized exchanges have API keys that allow traders to access market data in real time and execute trades from third party services. For example, an organization could develop a trading app and utilize a Binance API key to conduct trades through the platform. Usually, centralized exchanges disable the withdrawal permissions by default. However hackers are still able to abuse permissions through a number of techniques. For example, a cybercriminal could inflate the price of a worthless token and force the victims account into purchasing the inflated asset. The attacker is then able to withdraw valuable assets whilst the victim is left with a worthless token.
In the case of Kronos Research, we can see that EOA 0x6F15ee9258ACDEbf356dB7aB607bB255a00C6fdF receives USDT originating from Binance in multiple transactions, however it is not known what steps the attacker had to take in order to remove funds from Kronos Research CEX accounts.
Conclusion
The theft of sensitive information such as private keys have been driving the majority of losses this year. Approximately 57% of the overall losses in 2023 have originated from 40 private key compromises which is all the more concerning since we have accounted for 669 overall incidents. Centralized entities have been lucrative targets for cybercriminals over the past 11 months as the total value locked in DeFi protocols has been suppressed. Unfortunately, we will likely continue to see private key compromises causing substantial losses compared to exit scams and attacks on DeFi protocols throughout the remainder of the year.
