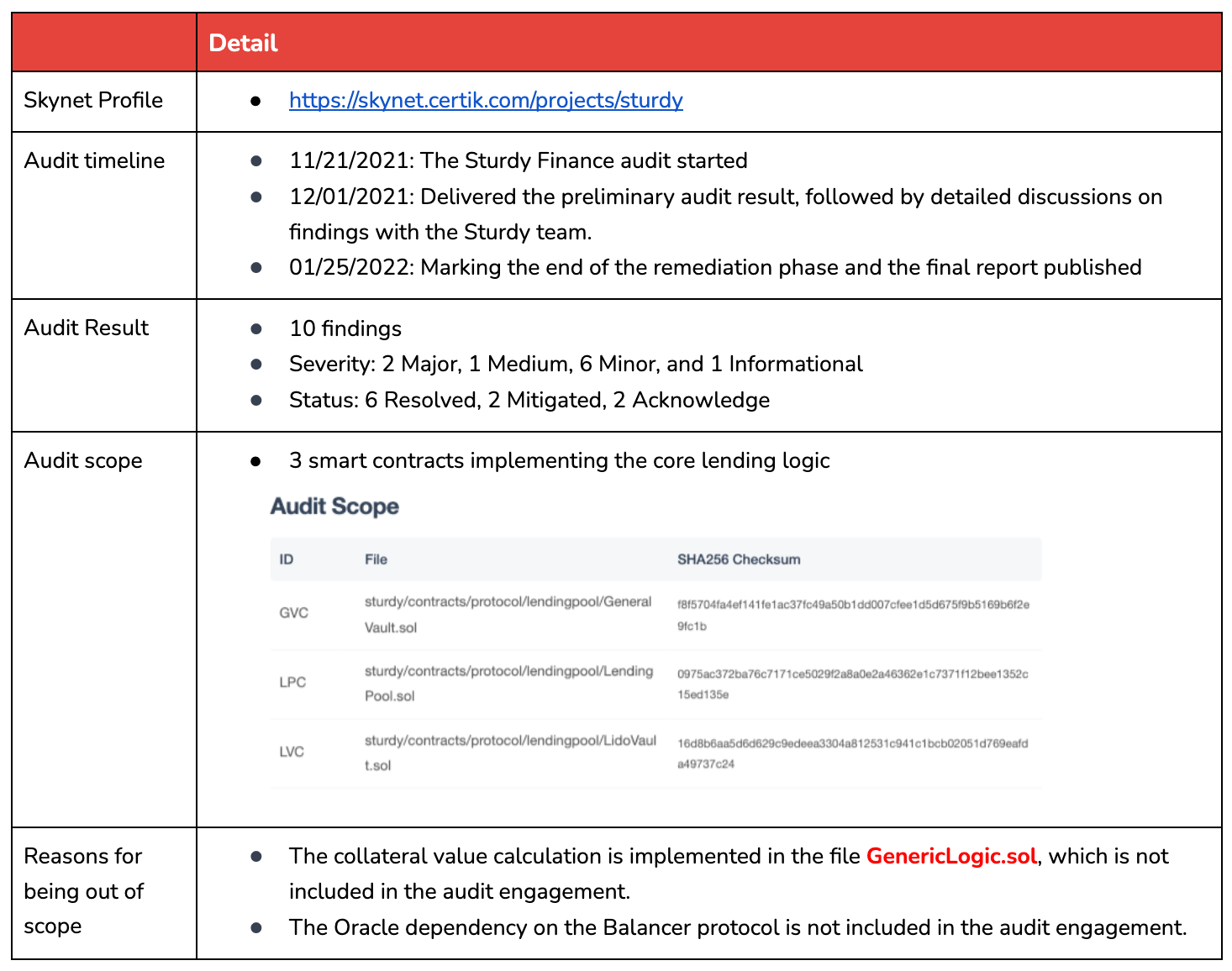
Project name: Sturdy Finance
Project type: Lending
Date of exploit: Jan 12, 2023
Asset loss: 442 ETH
Vulnerability: Price manipulation (read-only reentrancy)
Date of audit conducted: Jan 25, 2022
Conclusion: Out of audit scope
Details of the Exploit
Project Background
Sturdy Finance, a DeFi lending protocol, enables users to deposit collateral and borrow tokens based on their collateral value, which is determined by external price Oracles to acquire price for the collateral. In the recent exploit, the Balancer protocol functioned as this external price Oracle.
Nature of the Vulnerability
- The attacker's collateral value is incorrectly calculated by a manipulated asset price, so the attacker can borrow more than its collateral to drain the vault.
- The collateral price is provided by a Balancer protocol, which has a read-only reentrancy issue in its implementation.
- The attacker manipulated the collateral price from the Balancer protocol by triggering external calls to update its collateral in Sturdy's lending protocol in the process of withdrawing tokens from the Balancer protocol.
CertiK Audit Overview
Conclusion
On Jan 12, 2023, the lending platform Sturdy Finance was attacked, leading to a loss of 442 ETH. The attacker made use of a read-only reentrancy vector to manipulate the price used in a lending protocol to drain funds. The vulnerability lies in the dependency on the Balancer protocol, which was used to price Oracles in Sturdy's contracts and has been widely recognized by the community. The dependency on the Balancer protocol is not in CertiK's audit scope.
References
Rekt.new Analysis: https://rekt.news/sturdy-rekt/
Additional Resources: Reentrancy Vulnerability Scope Expanded