At CertiK, it’s our mission to raise the standard of security and transparency across the entire Web3 world. In light of this mission, and after listening to our users' feedback and recognizing the growing threat of centralization risks in the industry, we've made major upgrades to Skynet’s Web3 security analysis dashboards. We’ve taken centralization risks out of the shadows and made them much more accessible and legible, enabling users to spot potential hazards immediately.
No longer do you have to dig through audit reports (they’re complex, we get it) to find possible centralization issues. Now, Skynet puts centralization risk front and center.
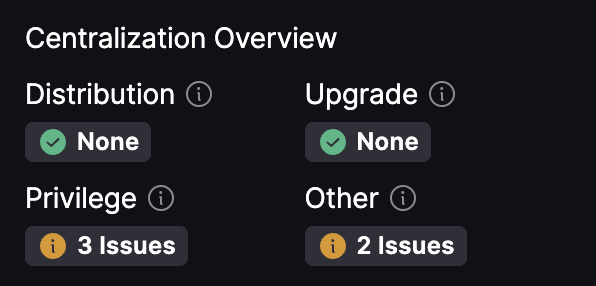
You’ll find a new Centralization Overview widget in the Code Security dashboard, right next to the audit report and findings. This overview makes it easy to see at a glance whether a smart contract has potential centralization issues.
Distribution: Either all or the majority of the tokens are transmitted to the contract deployer, or to one or more predetermined addresses. The activities of these addresses, such as trading, could significantly affect the value of the tokens.
Upgrade: Indicates that the contract owner can update the implementation contract behind the proxy, which will change the logic/behavior of the contract.
Privilege: Indicates that privileged roles possess the authority to control functions that can impact the project's operations or the core business logic.
Other: This category encompasses other vital but uncategorized operations that a privileged role can perform. These actions may potentially influence the user and their assets.
If a project has centralization risks flagged, it’s worth looking into the audit findings to understand the exact risk and whether the project owners have taken any steps to mitigate it. For a more comprehensive understanding, read through the technical audit report.
Skynet also includes a detailed Centralization Scanning dashboard, where you’ll find even more metrics to help you understand the level of centralization of a particular project.
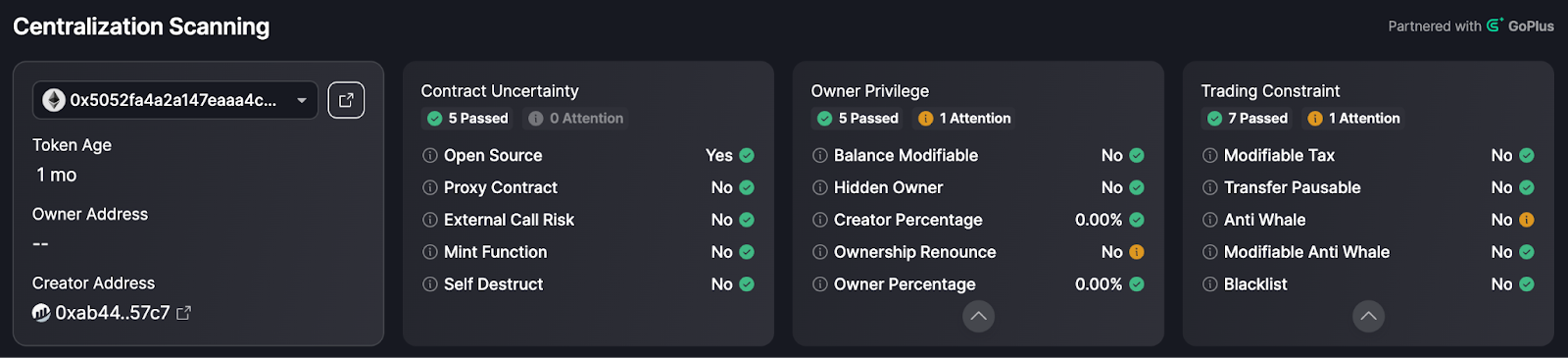
This dashboard introduces an array of new metrics, including:
- Whether the contract is open-source
- Whether there is a proxy contract
- Whether this contract has the ability to mint new tokens
- Whether the contract can self-destruct
- Whether contract ownership can be reclaimed
- Whether the contract owner has the authority to change the balance of any token holder
- Whether the contract has hidden owners
- The percentage of tokens held by the contract deployer
- Whether the contract owner has renounced its ownership of the contract
- Whether the contract is a honeypot
- Whether there are in-built trading taxes for buying and selling
- Whether these taxes can be modified
- Whether the contract has the function to limit the maximum amount of transactions or the maximum token holdings for an address
- Whether the token contract includes a blacklist function
…and more.
By putting centralization risk front and center, Skynet isn't just keeping pace with the ever-evolving landscape of Web3 security analysis, it's leading the way.
The updates don’t end there. Skynet’s Operational Resilience dashboard now includes a website security scan module.
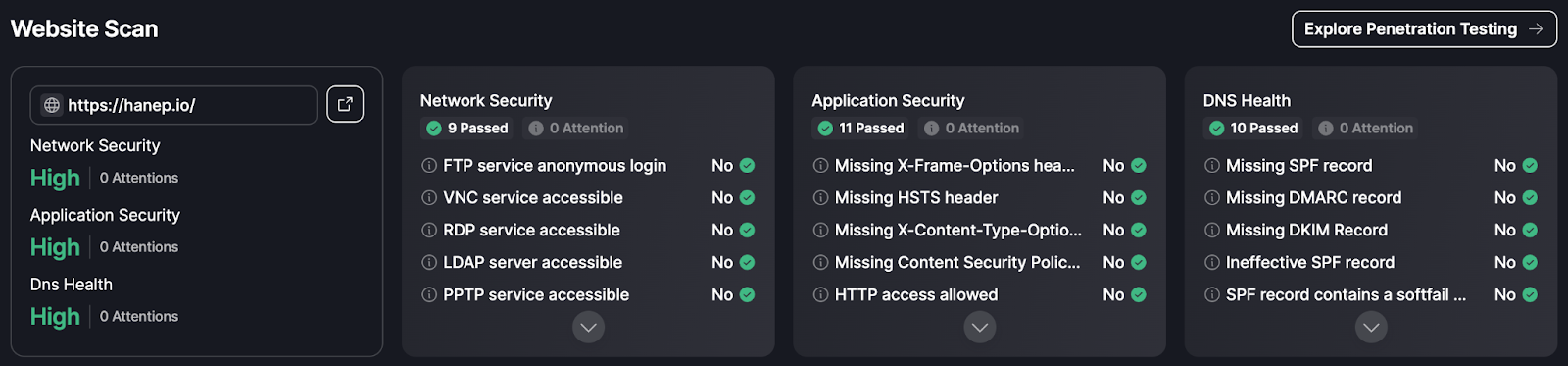
While the majority of security incidents in Web3 relate to smart contract exploits, front-end website security is just as critical as securing the contracts a platform runs on. The Website Scan module analyzes 30 different front-end security metrics and highlights any risks or suboptimal implementations encountered.
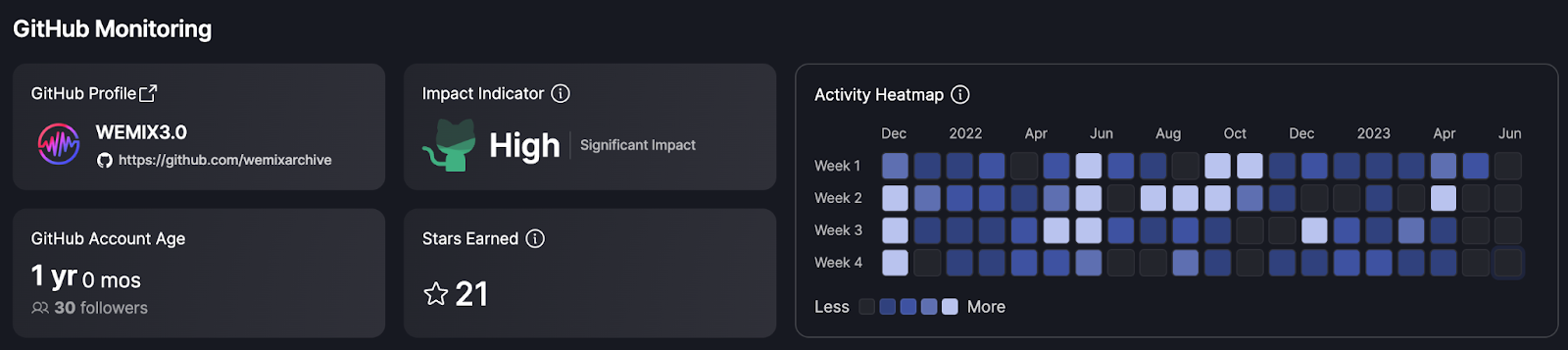
GitHub Monitoring showcases a platform's ongoing development efforts and the responsiveness of the team to fix issues. High activity levels often correlate with active and committed teams, indicating a healthier, evolving project which is likely to provide better security and an improved user experience.
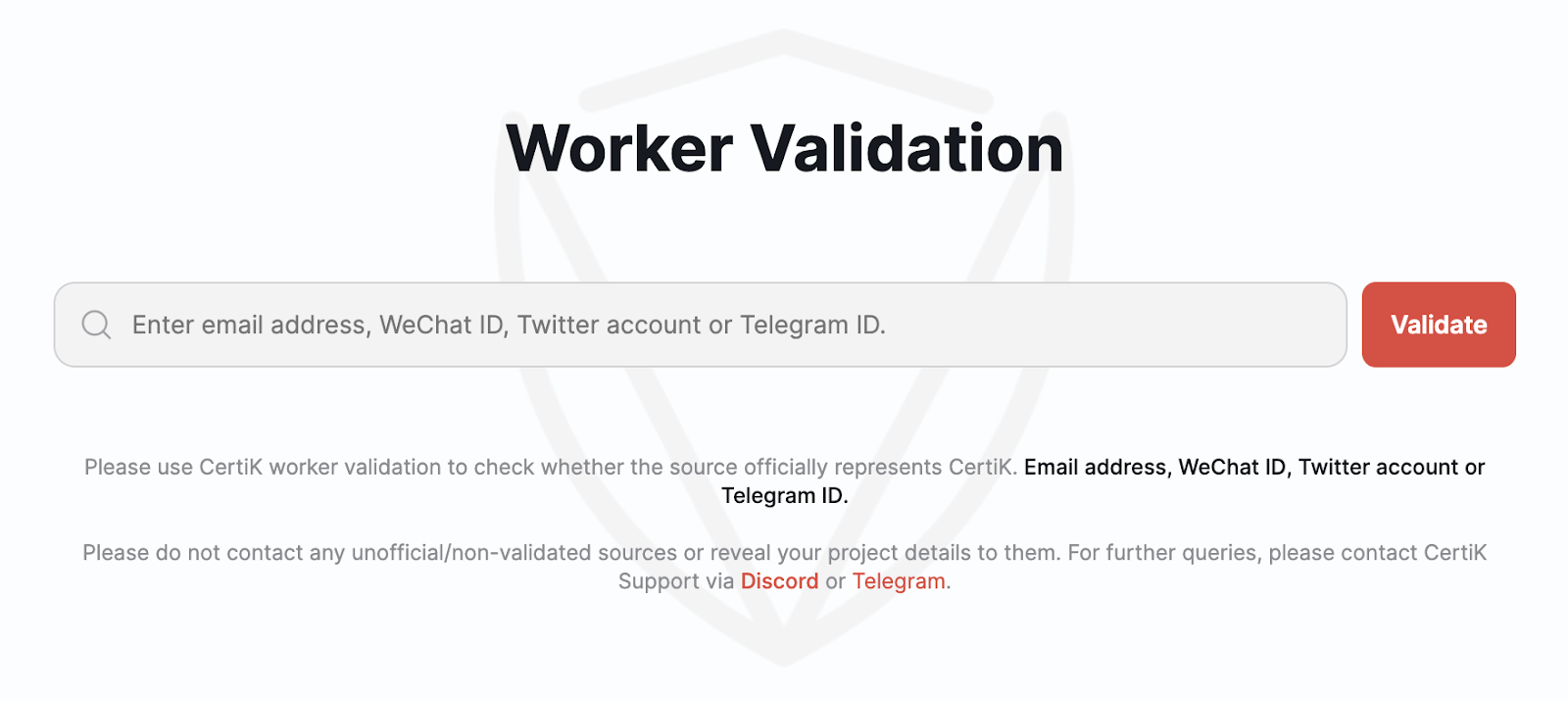
We’ve also introduced a new feature aimed at protecting the Web3 community from scammers. Our Worker Verification tool is being rolled out to help you avoid being scammed by fraudsters posing as CertiK employees. Now, you can verify the email address, WeChat ID, Twitter handle, or Telegram ID of anyone claiming to be contacting you on behalf of CertiK.
These new updates to the Skynet platform represent CertiK’s dedication to promoting transparency and security within the Web3 landscape. By making centralization risk unmissable, we are empowering users to make well-informed decisions, bypass the complexity of audit reports, and effectively mitigate potential hazards. We’re continuously refining and improving our free-to-use security tools based on the feedback of users, ensuring that Skynet’s security insights are the most comprehensive in the Web3 world. And we’re introducing a new tool to help protect our community from scammers who utilize our brand name to exploit their victims.